
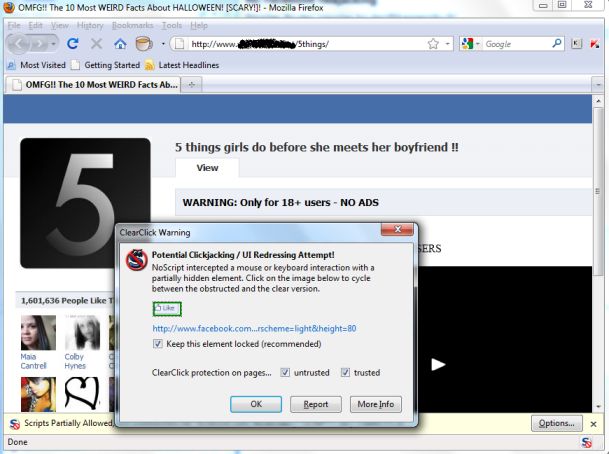
Another Facebook likejacking attempt is being spammed out to fool Facebook users with “5 things girls do before she meets her boyfriend”. Instead of presenting a video, the page redirects browsers to a “Like” button hosted on Facebook.
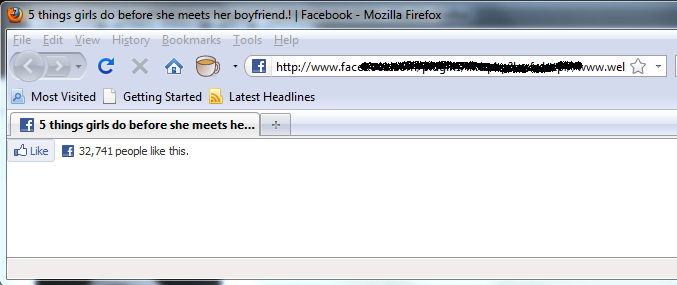
As illustrated above, tens of thousands of people have clicked on the link while they are logged into Facebook already. If you are one of the people who have already attempted to watch the video, please remove the “like” entry from your wall or newsfeed. Also, delete the liked page from your “Likes and Interests” section.
If you are using Facebook, be wary of what you click on. While this one may not be as serious an issue as some of the other Facebook scams we have seen, you probably don’t want to provide this plugin developer with more demographic statistics of who falls for phony videos.
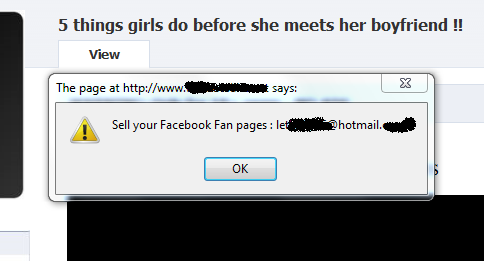
Even more interesting information falls out when you investigate a bit deeper. Attempting to access the “HTML source” results in an offer suggesting that you sell your fan pages to a suspicious email address, which is not recommended.






















Disliking Facebook LikeJacking