
Just another Sunday evening – I get to Moscow, check in and naturally go online to Facebook to inform everyone about how my trip went. Not very exciting, right? Wrong. A friend had ‘sent’ me a strange-looking link via Facebook IM. A closer look revealed that it was a link being spread by a new and active Facebook worm. The worm was stealing login credentials – and had already successfully stolen the credentials from thousands of people.
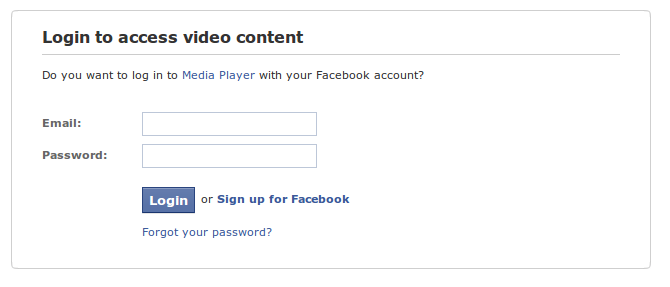
The worm spreads through Facebook instant messenger – just like many other Facebook worms. The message states the following: “Is this you?” followed by a link to the malicious Facebook app. The Facebook application is pretty simple; it loads new content into an iframe. The page which is loaded within the iframe is a simple phishing site: it asks for your Facebook credentials so that you can see some new content. Below is a screenshot of the login page:
I decided to investigate the phishing site a bit more, so I checked for some common directories on the server; directories which could contain more information about the worm and I found a directory which contained the Apache access logs. When analyzing the content of the log file I saw that someone was trying to access a file named acc.txt. I downloaded acc.txt and saw that the file contained stolen accounts: in the first version of acc.txt which I downloaded I saw that the attacker had collected over 3000 accounts! I downloaded the acc.txt at 5-minute intervals, and within 20 minutes, the number of stolen accounts went from 3000 to over 6000.
I immediately contacted the Facebook security team – who responded equally rapidly. The malicious page is down, and the Facebook team is going through their remediation routine.
This phishing attack was very simple and yet thousands of people fell for it!!! My guess is that there are lots of other similar attacks happening as I write this.
So… when you are logged on to Facebook, do NOT trust anything which is sent to you, especially not when it asks for your password or credit card information.




















Catching Facebook worms in Russia