
It’s the end of 2011 as we know it, and Microsoft feels fine finishing out the year with a handful of out-of-band holiday patches. This round is important not because the vulnerabilities directly impact massive numbers of customers and their online behavior on Windows laptops, tablets, and workstations, but because ASP.NET maintains vulnerable code enabling easy DoS of hosting websites, authentication bypass techniques, and stealth redirections to other websites (most dangerously those sites hosting phish and hosting client side exploits and spyware). All of this could curdle your eggnog in the coldest of weather.
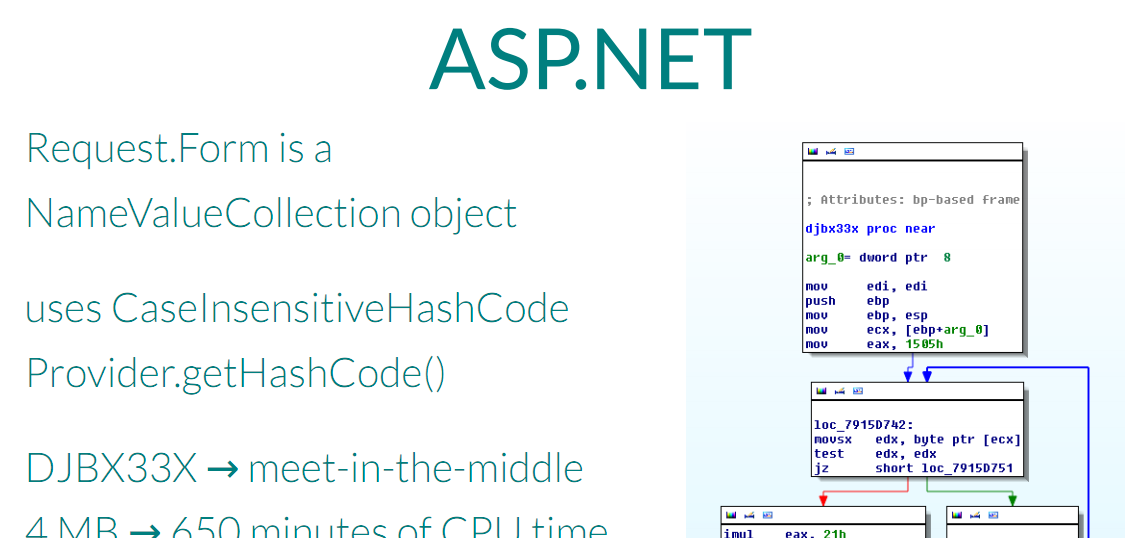
ASP.NET? Who really cares? Microsoft and its IIS web customers certainly do. With the huge number of distributed denial of service (DDoS) attacks coming not only from blackmailers and site competitors, but also the larger amounts of major news headline grabbing activity from hacktivist groups, the “recently disclosed” hashtable collision bug is important to IIS site operators that want to stay up and running.
This patch has been described as an “emergency” patch. But the disclosure coordination for the bug finders occurred back in late November (Nov 29th) for Microsoft, and November 1st for other vendors like PHP, Google, Oracle, Python, Ruby, etc. Perhaps the month/two month disclosure window provides some insight into the amount of time that it takes for these vendors to fix well-researched bugs. Also curious for this emergency bug is that Larry Wall and his Perl crew re-dev’d their hash table algorithms long ago, ensuring that their code isn’t vulnerable to these attacks. That work is all open source, and the developers of PHP 4 and 5, Java, Apache Tomcat, Apache Geronimo, Jetty, Oracle Glassfish, ASP.NET, Python, Plone, CRuby 1.8, JRuby, Rubinius, and v8 didn’t seem to take notice or made other tradeoffs, as their code is all vulnerable. A simple request sent to servers running any one of these frameworks could chew up the CPU at 100% for minutes, bringing the site to a screeching halt. Nonetheless, cheers to the Microsoft staff for reacting quickly over their holidays to fix this one. We hope that the other vendors can react quickly to this one as well, it seems to still be a lingering problem out there.
Also on deck are three other privately notified vulnerabilities, which may not have had as much of a splash in the media as the DoS attack because they weren’t dropped publicly at a well known con. The worst of these three bugs is probably the elevation of privilege (EoP) noted as the “ASP.Net Forms Authentication Bypass”. (It’s difficult to say which vulnerability is worse, but this one is rated “Critical” by Microsoft while the DoS vuln is rated “Important”.) While the attacker is required to register an account on the server and then target a user account that they know the name of, on most web servers that I’ve seen, that is not an insurmountable challenge by any means. From there, the attacker can send a request and assume the context of the targeted user account on the web server – at that point, they have the keys to the kingdom. It seems that the rush to cram an out-of-band set of patches would have more to do with a critical vulnerability like this one. The timing for these patches just seems unusual, considering that Microsoft is reporting that none of them are being used in attacks that they are aware of. But hey, if the patches are ready, might as well get them all out at once, instead of waiting for another cycle. The release timing most likely is just the sign of a mature development and deployment process.
The other two bugs are EoP and an unusual bug that enables attackers to redirect users from vulnerable web sites (which may be very, very popular) to malicious web sites of their choosing. While we haven’t seen extraordinary redirection volumes from well-known legitimate websites to malicious Blackhole sites or phishing sites, that is something we are watching right now.






















ASP.NET Holiday Patches