
Earlier today we intercepted a number of mailings with a new Warezov downloader. The good news is that it’s already detected as Email-Worm.Win32.Warezov.pk, which we added to our database two days ago.
What’s interesting about the mails is that along with the usual executable (which in this case is called “access.exe”) the messages have a couple of PDFs attached.
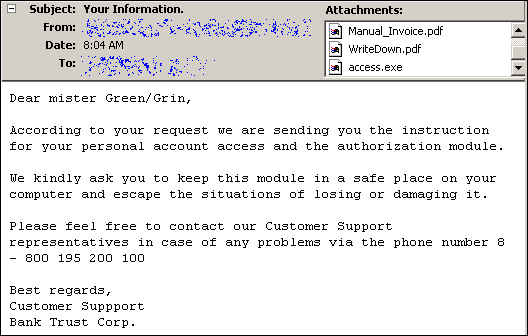
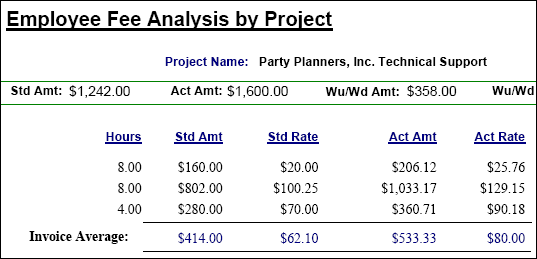
The PDFs, which are otherwise harmless, contain alleged financial transactions. Here’s an example:
If you get tricked by these and get to run the executable, it will contact kitinjderunhadsun.com and download another executable from there. This second exe is 91095 bytes in size, and we detect it as Email-Worm.Win32.Warezov.iq.
We detected the first version of Warezov almost one year ago and after all this time, the gang behind these worms is still roaming free. I’m really looking forward to the day they get caught.






















A green grin