
We’re starting to see a growth in the number of malicious programs which are being used to get money out of users – a type of cyber extortion.
Examples of this type of malicious program are Virus.Win32.GPCode, and Trojan.Win32.Krotten. Today we detected the latest modification of Krotten, Trojan.Win32.Krotten.n.
Trojan.Win32.Krotten uses exactly the same approach as GPCode. It corrupts data on the victim machine, and also displays a message saying that the data will be unencrypted once payment is received by the user/ author of the malicious program. Krotten differs from GPCode in that GPCode encrypted data saved to disk. Krotten corrupts the system registry. The author of Krotten offers to restore the corrupted data in return for a sum equivalent to approximately $5.
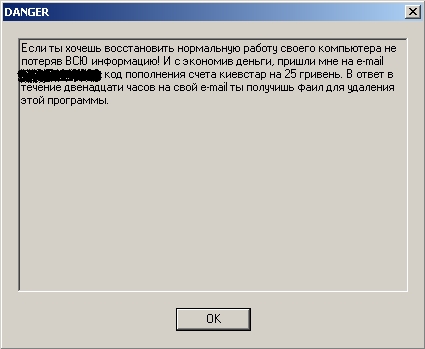
The Russian text states that within 12 hours following receipt of payment (to be sent to an email address given in the message) the user will receive a file which will delete the malicious program. The message, which mentions an account in Kiev, and specifies an amount in hryvnia, points to the Ukrainian origin of Krotten.
Detection for Trojan.Win32.Krotten.n has of course been added to our antivirus databases.
Once again, this is yet another case which shows that you should never open an unexpected attachment. And users should never send money to virus writers or those who are using them in cyber scams. This just encourages them to create a new version of whatever virus they are using, and launch another attack.





















Your money or your system registry