Little Discussion around Securing Windows 10
Microsoft presented a preview of their newest “experience”, Windows 10, over a live stream this morning. The release is expected later this year. This isn’t envisioned as just an OS for desktops, but it brings support as a truly broad computing platform. They claim to have built Windows 10 with “more personal computing” in mind, and it’s an ambitious push into seamlessly bringing together desktop computing, holographic computing (awesome!!!), mobile devices, gaming and IoT, a move to the “Store”, productivity applications, big data services and sharing, new hardware partner technologies, and cloud computing for a “mobility of experience”. They skimmed over “Trust” only in light of data privacy issues. From what I have seen, pushing aside security is a somewhat disappointing theme for all of the vendors at their previews, not just Microsoft. There is, however, a very long list of enhanced security features developed into this new codebase along with a massive amount of new attack surface introduced with this new platform.
Microsoft is attempting to better tighten down the new version of Windows the operating system by disallowing untrusted applications from installing and verifying their trustworthiness with their digital signature. This trusted signing model is an improvement, however, this active handling is not perfect. APT like Winnti’s attacks on major development shops and their multiple, other significant ongoing attack projects demonstrate that digital certificates are readily stolen and re-used in attacks. Not just their core group’s winnti attacks, but the certificates are distributed throughout multiple APT actors, sharing these highly valued assets, breaking the trust model itself to further their espionage efforts.
With seamless integration of all these data sharing services across computing resources, authentication and their underlying credentials and tokens cannot be leaked across services, applications, and devices. Pass-the-hash attack techniques frequently used by targeted attackers haunted corporate organizations using Windows for almost a decade. These types of credential theft techniques will have to be better protected against. And Flame introduced a whole new level of credential attack, so we may see Hyper-V and the newest container model for Windows 10 attacked to gain access to and abuse these tokens for lateral movement and data access. Defensive efforts haven’t been terribly successful in their responsiveness in the past, and Active Directory continues to see new attacks on organization-wide authentication with “skeleton keys”. So, their implementation of credential provisioning and access token handling will deserve security researchers’ attention – Hyper-V technologies and components’ attack surface will come under a new focus for years to come. And the DLP implementation for sharing corporate data securely is encouraging as well, but how strong can it be across energy constrained mobile hardware?
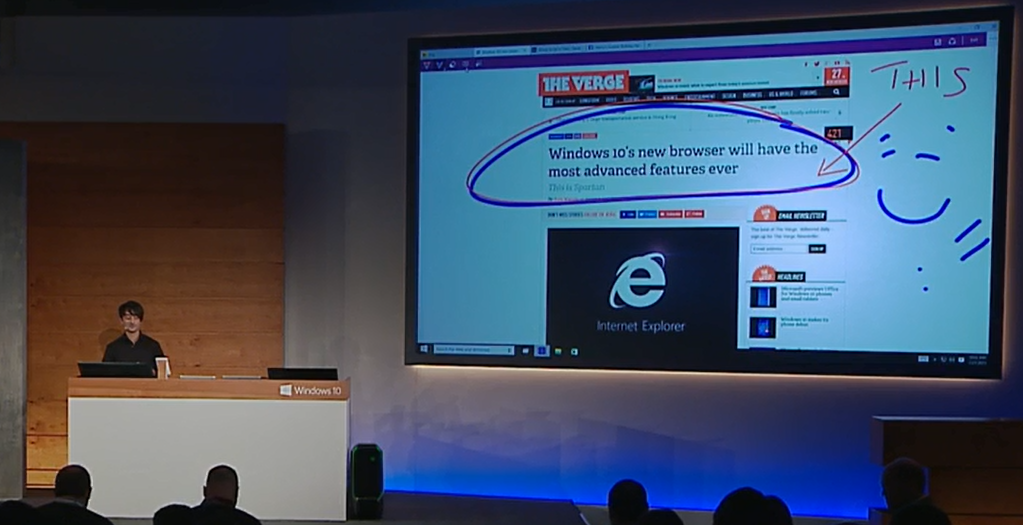
Considering that 2014 brought with it over 200 patch-worthy vulnerabilities for the various versions of Internet Explorer, a minimalist refresh of this code with the “Project Spartan” browser would be welcome. Simply put, the IE web browser was hammered in 2014 across all Windows platforms, including their latest. Our AEP and other technologies have been protecting against exploitation of these vulnerabilities in high volume this past year. Not only has its model implementing ActiveX components and its design been under heavy review, but the slew of newer code and functionality enabling “use-after-free” vulnerabilities led to critical remote code execution. The new Spartan browser brings with it large amounts of new code for communications and data sharing, which brings with it Microsoft’s track record of introducing hundreds of patch-worthy vulnerabilities annually into their browser code. Hopefully their team won’t bring that baggage with them, but the load seems pretty heavy with the new functionality. I didn’t see any new security features, development practices, or sandboxes described for it and will wait to see what is in store here.
An unusually large amount of time was set aside to present their “intelligent assistant” Cortana, which started with a somewhat disconnected and bizarre conversation between the presenter and the actual Cortana assistant instance onstage. The devil is in the details when implementing security support for access to data across fairly unpredictable services like this one.
Of course, our products are ready to go. Modern versions of Kaspersky Lab consumer products support Windows 10. The details are available here.
Windows 10 Preview and Security





















Samural
Not video preview and security of the windows 10?