
We just received a spam message in Portuguese stating the following:
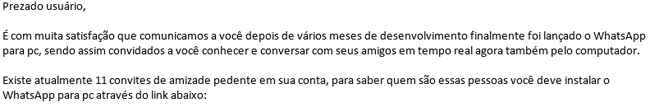
In short, this message says that WhatsApp for PC is finally available and that the recipient already has 11 pending invitations from friends in his account. This is what the email looks like:

If the victim clicks on the link, it will lead him/her to a hacked server in Turkey and will then be redirected to a Hightail (Yousendit) account to download the initial Trojan, which in the system looks like a 64 bitsinstallation file:

In reality, it is a standard 32 bits app with a moderate VT detection:
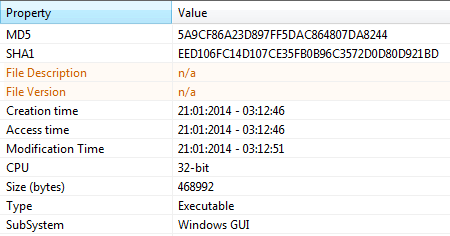
This downloader has some anti-debugging features like: UnhandledExceptionFilter() andRaiseException() and once running, it downloads a new Trojan that is banker itself. This time the malware comes from a server in Brazil and has a low VT detection 3 of 49. The recently downloaded banker has the icon of an mp3 file. Most users would click on it, especially after seeing it is about 2.5Mb in its weight.

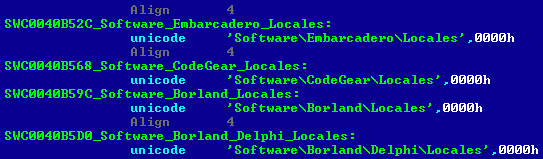
It also has some anti-debugging features to make its analysis harder. It’s written in Delphi XE5 from Embarcadero:
Once running, the malware reports itself to the cybercriminals’ infections statistics console and when open, a local port 1157 sends stolen information in the Oracle DB format. In addition, it downloads new malware into the system; some samples are 10Mb in size. This is the classic style of a Brazilian-created malware.
Kaspersky Anti-Virus detects all mentioned samples heuristically. Please stay alert, be aware and do not become a victim.
You may follow me on twitter: @dimitribest
WhatsApp for PC – a Guaranteed Trojan Banker






















Dee Schaffer
Is there a reliable removal system for this. I never completely downloaded it, but I have had problems since opening the site. I have a lot of malware on a brand new computer and problems with goggle chrome. I really don’t want to completely clean out my computer, but may have to do so.