
During the preparation of the “IT threat evolution Q2 2017” report I found several common Trojans in the “Top 20 mobile malware programs” list that were stealing money from users using WAP-billing – a form of mobile payment that charges costs directly to the user’s mobile phone bill so they don’t need to register a card or set up a user-name and password. This mechanism is similar to premium rate SMS messages but Trojans do not need to send any SMS in this case – they just need to click on a button on a web-page with WAP-billing.
From user’s perspective a page with WAP-billing looks like regular web-page. Usually such pages contain complete information about payments and a button. By clicking on this button user will be redirected to a mobile network operator server, which may show additional information and request user’s final decision about payment by clicking on another button. If the user connects to the Internet through mobile data, the mobile network operator can identify him/her by IP address. Mobile network operators charges users only if they are successfully identified and only after click on the button.
From a financial point of view, this mechanism is similar to the Premium rate SMS service – charge is directly applied to users’ phone bills. However, in this case Trojans do not need to send any SMS – just to click on button on a web-page with WAP-billing.
We hadn’t seen any Trojans like this in a while, but several of them appeared out of nowhere. Different Trojans from different cybercriminal groups targeting different countries (Russia and India) became common at the same time. Most of them had been under development since the end of 2016 / the beginning of 2017, but their prevalence increased only in the second half of Q2 2017. Therefore, I decided to take a closer look at these Trojans.
In general, these Trojans are doing similar things. First, they turn off WiFi and turn on mobile Internet. They do this because WAP-billing works only through mobile Internet. Then they open a URL which redirects to the page with WAP-billing. Usually, Trojans load such pages and click on buttons using JavaScript (JS) files. After that they need to delete incoming SMS messages containing information about subscriptions from the mobile network operator.
Furthermore, some of them have the ability to send premium rate SMS messages. In addition, some are exploiting Device Administrator rights to make it harder to delete the Trojan.
Trojan-Clicker.AndroidOS.Ubsod
I started with Trojans that are detected as Trojan.AndroidOS.Boogr.gsh. These files are recognized as malicious by our system, based on machine learning algorithms. The most popular files detected in Q2 2017 by ML detection were Trojans abusing WAP-billing services. After analyzing them, I found that they belong to the Trojan-Clicker.AndroidOS.Ubsod malware family.
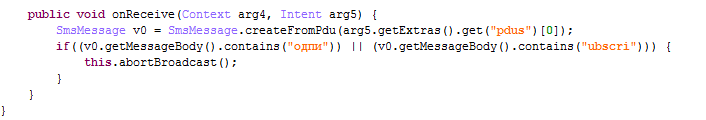
It is a small and simple Trojan that receives some URLs from its command and control server (CnC) and opens them. These URLs could just be AD URLs where the Trojan pretends that it is a type of advertising software by using class names like “ViewAdsActivity”. But, it can delete all incoming SMS messages that contain the text “ubscri” (part of “Subscription”) or “одпи” (part of “Подписка”, Subscription in Russian). Furthermore, it can turn off WiFi and turn on mobile data. Trojans need this because WAP-billing only works when the page is visited through mobile internet, not through WiFi.
After analyzing these Trojans, I found that some of them (MD5 A93D3C727B970082C682895FEA4DB77B) also contain a different functionality – to decrypt and load (execute) additional executable files. This functionality is detected as Trojan-Dropper.AndroidOS.Ubsod. These Trojans, in addition to stealing money through WAP-billing services, were also executing another Trojan, detected as Trojan-Banker.AndroidOS.Ubsod.
An interesting thing about Trojan-Banker.AndroidOS.Ubsod was that it was distributed not only in other Trojans, but also as a standalone Trojan (MD5 66FE79BEE25A92462A565FD7ED8A03B4). It is a powerful Trojan with lots of capabilities. It can download and install apps, overlay other apps with its windows (mostly to steal credentials or credit card details), show ads, send SMS messages, steal incoming messages and even execute commands in the device shell. Furthermore, it has features that steal money by abusing WAP-billing services, which mean that in some cases infected users had two Trojans attacking the same thing.
According to KSN statistics it was the most popular of all such Trojans, with almost 8,000 infected users in July 2017 from 82 countries. 72% of attacked users were in Russia.
Xafekopy
Another malware family that has become popular during the last few months is Trojan-Clicker.AndroidOS.Xafekopy. This Trojan uses JS files to click on buttons on web-pages containing WAP billing to silently subscribe users to services. The most interesting thing is that these JS files look similar to Ztorg’s module JS files; they even have the same names for some functions. This Trojan was created by some Chinese-speaking developers (just like Ztorg) but mainly attacks Indian (37%) and Russian (32%) users.
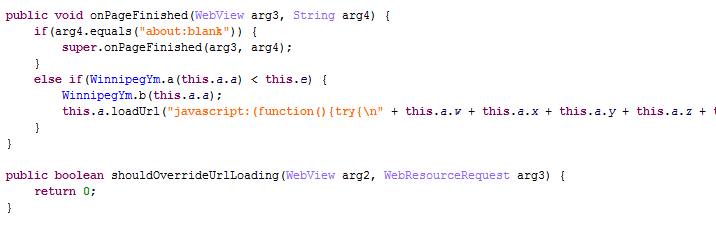
This Trojan is distributed through ads masquerading as useful apps, mostly as battery optimizers. After installation, it acts like a useful app but with one difference – it loads a malicious library. This library decrypts and loads files from the assets folder of the installation package. These files decrypt and load another file from the assets folder which contains the main malicious functionality. It decrypts (yep, decryption again) JS files. Using these JS files it can bypass captcha forms and click on web-pages with WAP billing. By doing so it steals money from a user’s mobile accounts. It can also click on some ad pages to make money from ads.
The files with the main functionality (which was decrypted) contain URLs with WAP-billings. I was able to find only two different versions of this file – one version contains Indian links, another – Russian links.
It also can send SMS messages (most likely premium rate SMS). It steals incoming SMS messages and deletes some (most likely AoC messages).
According to KSN statistics, almost 40% of attacked users were in India, but in total we saw it attacking more than 5,000 users from 48 different countries in July 2017.
Autosus
The main purpose of Trojan-Clicker.AndroidOS.Autosus.a is to steal a user’s money by clickjacking pages with WAP-billing. To do so, the Trojan receives the JS file and URL to click on. It also can hide from user’s incoming SMS using rules received from the CnC.
After starting, the Trojan will ask the user to activate device administrator rights for this Trojan. After that, the Trojan will delete its icon from the app list so users won’t be able to easily find it. Meanwhile the Trojan will continue working in the background, receiving its CnC commands to open URLs and click on buttons.
This Trojan attacked more than 1,400 users in July 2017, most of them were from India (38%), South Africa (31%) and Egypt (15%).
Podec
When talking about clickjacking WAP-billing services, we should mention Trojan-SMS.AndroidOS.Podec.a. This Trojan – initially found in 2014 – was a regular Trojan-SMS until 2015, when cybercriminals switched to attacking WAP-billing services. This Trojan has lots of functionality but its main task is to steal money by subscribing users to WAP services. It was the first mobile Trojan that was able to bypass captcha. Over the next few years it became of the most popular mobile Trojans. It’s last appearance in the top 20 most popular mobile Trojans was in Q2 2016.
Podec is still actively distributing, mainly in Russia. It was the third most common Trojan in June 2017, among other Trojans abusing WAP-billings.
Conclusion
During last few months, we have detected a growth of Trojans attacking WAP-billing services in different countries. Although Trojans with such functionality have been infecting users for years, we see, that there are several new Trojans, and the number of infected users has been significantly increased in recent months. Furthermore, previously WAP-billing services were under attack mostly in Russia, but now we have detected such attacks in different countries, including India and South Africa.
Even some Trojans which traditionally specialized in other attacks, started stealing users’ money by clickjacking WAP-billing services.
We weren’t able to find a reason why so many cybercriminals decided to switch or to start attacking WAP-billing services at the same time. WAP-billing services are not a new thing – in some countries they’ve been existed for several last years.
MD5
F3D2FEBBF356E968C7310EC182EE9CE0
9E492A6FB926E1338DADC32463196288
A93D3C727B970082C682895FEA4DB77B
66FE79BEE25A92462A565FD7ED8A03B4
AEAE6BFDD18712637852C6D824955859
DA07419994E65538659CD32BF9D18D8A
WAP-billing Trojan-Clickers on rise




























Jacqui
Do Kaspersky Lab have any solutions to filter out this sort of fraud?
Jeffrey
This article has no solutions.