
It’s February, and that means Valentine’s Day-related spam. Lots of it! There are already loads of adverts offering expensive alcohol and chocolates, jewellery and leather goods, romantic trips for two etc.
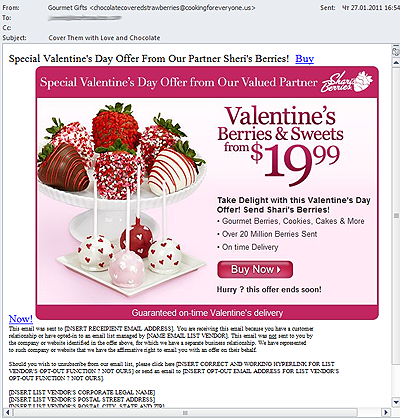
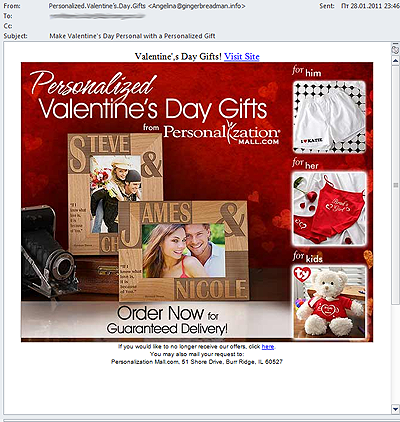
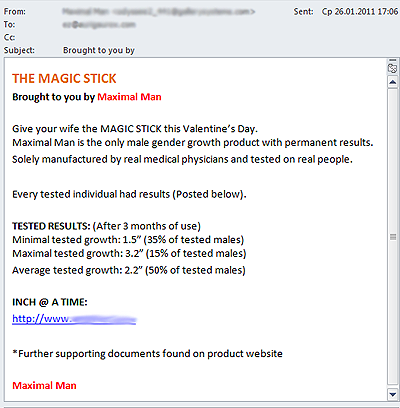
Other goods that are traditionally advertised in spam, such as fake designer watches and Viagra, have also exploited the Valentine’s Day theme to grab the attention of email recipients. The spammers appear convinced that there’s no better time than 14th February to increase your libido or buy cheap replicas of designer watches:
So far, this year’s Valentine’s Day spam has been mostly harmless, but we would like to warn our readers once again that the first half of February usually sees a surge in malicious links appearing in emails that appear to be for virtual greeting cards. So, be careful if you receive an e-card – make sure it has come from a genuine source before clicking any links.
Kaspersky Lab will be following developments closely in the run-up to Valentine’s Day.



















Valentine’s spam on the increase