
Just few hours ago Twitter officially announced the launch of their new iPhone application called “Twitter for iPhone”. The news quickly became a trendy topic in Twitter and as it used to be the criminals took advantage of this one more time. The difference this time is that the criminals behind this particular attack didn’t want to use Rogue AV malware but a Worm with dropper functions to deliver Trojan banker malware to the users machine.
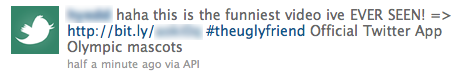
This is an example of detected malicious twitts by us:
The initial Trojan is downloaded to the victim machine by a malicious Java archive file. It has several malicious features, for example: spreading through USB devices; it disables Windows task manager, the regedit application and also notifications from Windows Security Center. Also it creates a copy of itself in the system with the name of Live Messenger. The criminals even included an anti-virtualization feature. The worm checks if the hard drive of infected system is virtualized or not. If found to be in a virtual system, the malicious code won’t be executed.
As I mentioned the main goal of this Trojan is to steal on-line bank credentials of the victims!
This malware is very harmful since credit cards and on-line banking credentials are in the game. Please, be really careful specially with trend topics (searches) since in many cases they are being used by criminals.
Kaspersky Anti-Virus detects the threat as Worm.Win32.VBNA.b






















Twitter for iPhone ™ and unexpected malicious results