
It’s often argued that *nix systems are secure, and there aren’t any viruses or malware for such systems. This hasn’t been true for a long time, as two recently detected malicious programs prove.
The first is Trojan-Mailfinder.Perl.Hnc.a, a perl script which connects to a command server to get text and a recipient list for spam mailings.
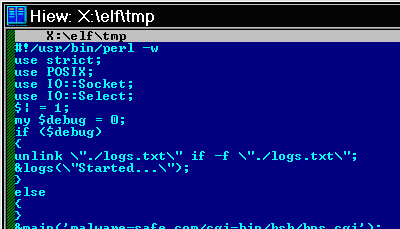
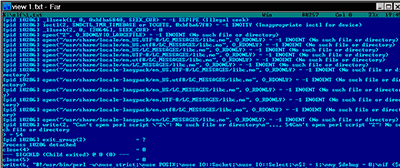
The second program is Trojan-Dropper.Linux.Prl.a, an executable for Linux and FreeBSD. The file decrypts the perl script, launches the perl interpreter and then gives it the decrypted script.
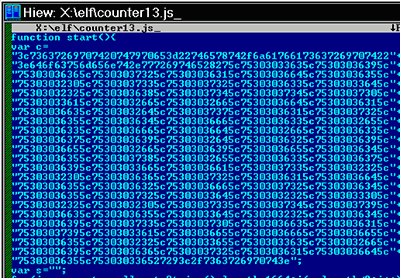
This malware has been detected on servers infected with Trojan-Downloader.JS.Iframe.auy (shown in the screenshot below).
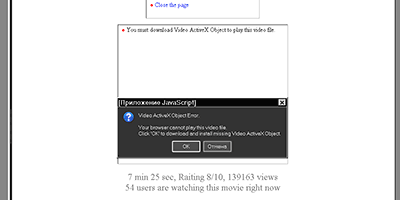
This redirects site visitors to a site that will download exploits and other malicious programs in the guise of a video codec:
The site which spreads spam also contains a page advertising a rogue antivirus which claims it will clean the user’s computer for $60. (We classify the rogue app as not-a-virus:FraudTool.Win32.MalwareDoctor.e):
At the moment we know of around 1000 cases of sites infected with Trojan-Downloader.JS.Iframe.auy. There are also several hundred servers infected with Trojan-Mailfinder.Perl.Hnc.a and Trojan-Dropper.Linux.Prl.a, which are actively spreading spam.
The days of *nix systems not being targeted by malware writers are long gone. In my view, admins need to wake up; they should be on top of all of today’s threats, rather than letting their systems – and worse, visitors to their sites – get infected. Shame on you, guys.























The myth of *nix security