
In a nutshell
- Backdoor.OSX.Mokes.a is the most recently discovered OS X variant of a cross-platform backdoor which is able to operate on all major operating systems (Windows,Linux,OS X). Please see also our analysis on the Windows and Linux variants.
- This malware family is able to steal various types of data from the victim’s machine (Screenshots, Audio-/Video-Captures, Office-Documents, Keystrokes)
- The backdoor is also able to execute arbitrary commands on the victim’s computer
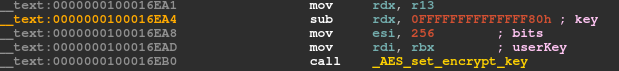
- To communicate it’s using strong AES-256-CBC encryption
Background
Back in January this year we found a new family of cross-platform backdoors for desktop environments. After the discovery of the binaries for Linux and Windows systems, we have now finally come across the OS X version of Mokes.A. It is written in C++ using Qt, a cross-platform application framework, and is statically linked to OpenSSL. This leads to a filesize of approx. 14MB. Let’s have a look into this very fresh sample.
“Unpacked” Backdoor.OSX.Mokes.a
Its filename was “unpacked” when we got our hands on it, but we’re assuming that in-the-wild it comes packed, just like its Linux variant.
Startup
When executed for the first time, the malware copies itself to the first available of the following locations, in this order:
- $HOME/Library/App Store/storeuserd
- $HOME/Library/com.apple.spotlight/SpotlightHelper
- $HOME/Library/Dock/com.apple.dock.cache
- $HOME/Library/Skype/SkypeHelper
- $HOME/Library/Dropbox/DropboxCache
- $HOME/Library/Google/Chrome/nacld
- $HOME/Library/Firefox/Profiles/profiled
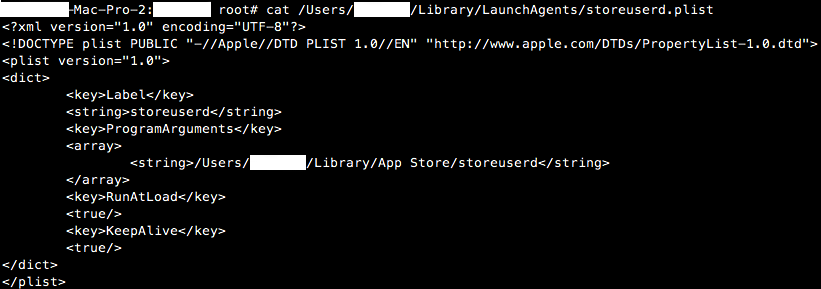
Corresponding to that location, it creates a plist-file to achieve persistence on the system:
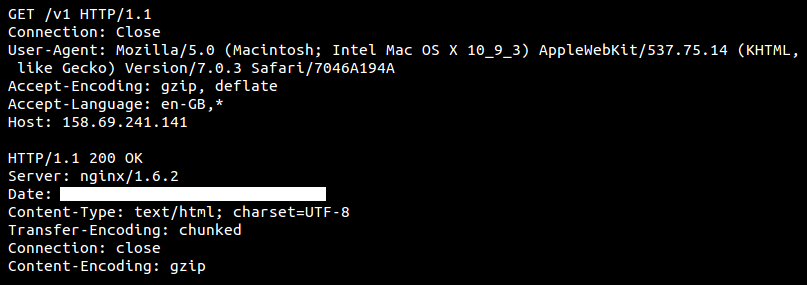
After that it’s time to establish a first connection with its C&C server using HTTP on TCP port 80:
The User-Agent string is hardcoded in the binary and the server replies to this “heartbeat” request with “text/html” content of 208 bytes in length. Then the binary establishes an encrypted connection on TCP port 443 using the AES-256-CBC algorithm.
Backdoor functionality
Its next task is to setup the backdoor features:
- Capturing Audio
- Monitoring Removable Storage
- Capturing Screen (every 30 sec.)
- Scanning the file system for Office documents (xls, xlsx, doc, docx)
The attacker controlling the C&C server is also able to define own file filters to enhance the monitoring of the file system as well as executing arbitrary commands on the system.
Just like on other platforms, the malware creates several temporary files containing the collected data if the C&C server is not available.
- $TMPDIR/ss0-DDMMyy-HHmmss-nnn.sst (Screenshots)
- $TMPDIR/aa0-DDMMyy-HHmmss-nnn.aat (Audiocaptures)
- $TMPDIR/kk0-DDMMyy-HHmmss-nnn.kkt (Keylogs)
- $TMPDIR/dd0-DDMMyy-HHmmss-nnn.ddt (Arbitrary Data)
DDMMyy = date: 070916 = 2016-09-07
HHmmss = time: 154411 = 15:44:11
nnn = milliseconds
If the environment variable $TMPDIR is not defined, “/tmp/” is used as the location (http://doc.qt.io/qt-4.8/qdir.html#tempPath).
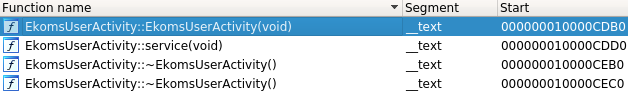
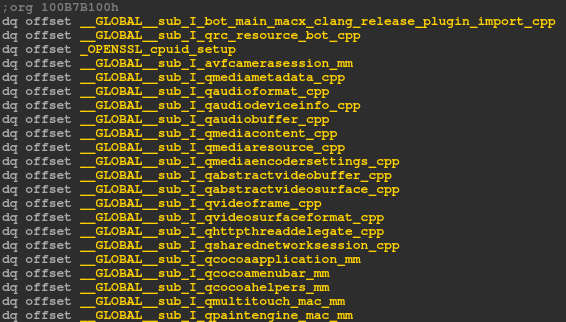
Hints from the author
The author of this malware again left some references to the corresponding source files:
Detection
We detect this type of malware as HEUR:Backdoor.OSX.Mokes.a
IOCs
Hash:
664e0a048f61a76145b55d1f1a5714606953d69edccec5228017eb546049dc8c
Files:
$HOME/LibraryApp Store/storeuserd
$HOME/Library/com.apple.spotlight/SpotlightHelper
$HOME/Library/Dock/com.apple.dock.cache
$HOME/Library/Skype/SkypeHelper
$HOME/Library/Dropbox/DropboxCache
$HOME/Library/Google/Chrome/nacld
$HOME/Library/Firefox/Profiles/profiled
$HOME/Library/LaunchAgents/$filename.plist
$TMPDIR/ss*-$date-$time-$ms.sst
$TMPDIR/aa*-$date-$time-$ms.aat
$TMPDIR/kk*-$date-$time-$ms.kkt
$TMPDIR/dd*-$date-$time-$ms.ddt
Hosts:
158.69.241[.]141
jikenick12and67[.]com
cameforcameand33212[.]com
User-Agent:
Mozilla/5.0 (Macintosh; Intel Mac OS X 10_9_3) AppleWebKit/537.75.14 (KHTML, like Gecko) Version/7.0.3 Safari/7046A194A
The Missing Piece – Sophisticated OS X Backdoor Discovered


























Peter
Then you have to inform the people never to lower your defence shields of your Mac.
If you do that, well yes, than you can install everything. But you do not mention this.
Patrick
How do you get rid of it?
Stefan Ortloff
Unless there’s no other previously installed malware or malware dropped by that backdoor present on the system, deleting the binary cures the infection.
Geoffrey Hale
Any idea who was behind this project?
Greg Slepak
These locations are incorrect:
$HOME/Library/App Store/storeuserd
$HOME/Library/com.apple.spotlight/SpotlightHelper
$HOME/Library/Dock/com.apple.dock.cache
$HOME/Library/Skype/SkypeHelper
$HOME/Library/Dropbox/DropboxCache
$HOME/Library/Google/Chrome/nacld
$HOME/Library/Firefox/Profiles/profiled
That should say:
$HOME/Library/Application Support/App Store/storeuserd
$HOME/Library/Application Support/com.apple.spotlight/SpotlightHelper
$HOME/Library/Application Support/Dock/com.apple.dock.cache
$HOME/Library/Application Support/Skype/SkypeHelper
$HOME/Library/Application Support/Dropbox/DropboxCache
$HOME/Library/Application Support/Google/Chrome/nacld
$HOME/Library/Application Support/Firefox/Profiles/profiled
Stefan Ortloff
I can’t confirm incorrectness. Locations mentioned in the article were tested on OS X 10.8.2.
eugene
The function name references are references to the Qt library. I’m surprised they figured out how to compile that statically.
JayB
Shouldn’t the directories be in $HOME/Library/Application\ Support ??
Stefan Ortloff
I can’t confirm. Locations mentioned in the article were tested on OS X 10.8.2. “The Application Support directory is where your app stores any type of file that supports the app but is not required for the app to run, such as document templates or configuration files.” (https://developer.apple.com/library/mac/documentation/General/Conceptual/MOSXAppProgrammingGuide/AppRuntime/AppRuntime.html)
Ken
Misleading title. This is not an OS X backdoor.
Pedro Smith
How can someone get infected with this?
Stefan Ortloff
Since we only got the binary itself, we can only speculate how this malware makes it to the victim machine. All vectors are possible: exploits, installation via another previously installed malware and of course via social engineering.
Tim Keller
Yes this is a payload not an exploit. That’s what a backdoor is. You could also call it a RAT. This is the thing you install after you’ve compromised the system using whatever technique you made work. Unless you know the vector that was used to get it onto your system (the exploit) there’s no point in doing anything other than reinstalling from known good media, updating to the latest patch level & installing security software including an application firewall (Little Snitch, https://www.obdev.at/products/littlesnitch/index.html ) & malware detection & prevention software like the stuff from Objective See https://objective-see.com/index.html & Jonathan Zdiarski’s newly released Little Flocker http://www.zdziarski.com/blog/?page_id=6171 . Do all of that properly & you should be fine.
anon
jikenick12and67[.]com
found this
s:853e9a42efca88ae0dd1a83aeb215047