
Cryptocurrency has gradually evolved from an element of a new world, utopian economy to a business that has affected even those sectors of society least involved in information technology. At the same time, it has acquired a fair number of “undesirable” supporters who aim to enrich themselves at the expense of other users: attackers who release miners embedded in user JS scripts, or plan to implement miners into IoT devices at the production stage; hidden in countless variations of Trojans in conjunction with SMB exploits etc.
We will tell you two unusual success stories that happened on the “miner front”. The first story echoes the TinyNuke event and, in many respects gives an idea of the situation with miners. The second one proves that to get crypto-currency, you don’t need to “burn” the processor.
DiscordiaMiner and fights on forums
In early June, our analysts found a new and seemingly unremarkable Trojan that unloaded the miner of the popular Monero crypto-currency. However, in the course of further research, we uncovered many interesting details that we would like to share with you.
Kaspersky Lab products detect this Trojan as Trojan.Win32.DiscordiaMiner. It works as follows:
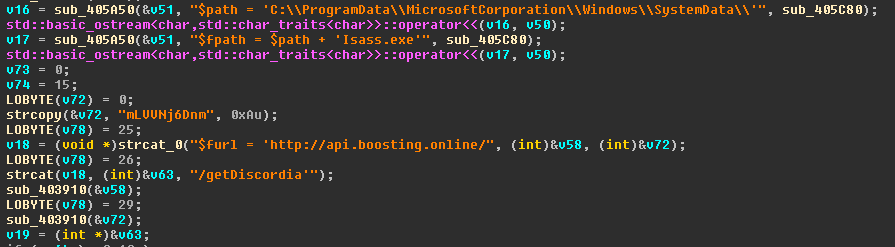
- Creates a number of directories in the system to download the necessary files;

- Copies itself in C:\ProgramData\MicrosoftCorporation\Windows\SystemData\Isass.exe;
- Gets the update from the server;
- Creates an autorun task;

- Gets the miner files;

- Gets the credentials of the user in whose name it wants to run the mining;
- Starts the miner.
All interaction with the command server (C&C) occurs in the open, with the help of GET requests, without any check or verification. In all samples, the hxxp://api[.]boosting[.]online address is provided as the C&C. The line associated with the individual user (etc. MTn31JMWIT) and the address of the required resource – the list of files, the update, etc. – are added to the server address. Example: hxxp://api[.]boosting[.]online/MTn31JMWIT/getDiscordia
Discord on the forum
As mentioned above, at a certain point in its work, the Trojan is instructed to issue a command to run the miner: it specifies the email of the user who has “done the job”. It looks like this:
-user <user_email> -xmr
Using the value of the <user_email> argument, with the first line of the search results we get the Trojan-related topic on the Russian-language forum:
On this forum thread there is a wide discussion of the Trojan’s work details. The most interesting part of the discussion is on page 21 – the forum participants accuse the Trojan’s author of substituting users’ addresses with his own. Among other things, there is also a dialogue on the chat app, Telegram where the author explains this substitution as a banal mistake.
On the forum, the author of DiscordiaMiner references the short lifespan of this error as an argument in his defense:
He also mentions the figure of 200,000 infected machines. It is difficult to say how true this is. However, in the malware samples we received, the email that the “prosecutor” refers to is often named. Examples of other addresses: ilya-soro*****12@mail.ru, v*****re@gmail.com, topne*****arin@gmail.com, J ***** m @ yandex.ru, steamfa*****aunt1@mail.ru, me*****ook@gmail.com, x*****z@yandex.ru, piedmont ***** lines @ yahoo. com.
Among other things, in the course of the dispute the author mentions that the source codes of the Trojan DiscordiaMiner are now publicly available.
Indeed, the first line of the search results provides the link to the author’s repository.
In addition to the source codes, which really do coincide fully with the restored Trojan code, the repository also includes very informative diagrams of the Trojan’s operation, the samples of documents used for distribution as well as instructions for how exactly the UAC is to be bypassed. The pictures below are taken from the repository (which is currently unavailable).
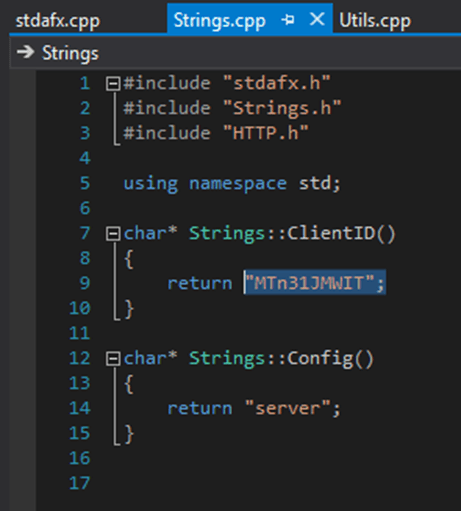
The source codes are presented in full and, apparently, only the user-associated string (ClientID) varies from assembly to assembly.
Although the “dumping” of program source code is not unique, this case in many respects echoes the NukeBot story – the same disputes on a forum followed by the publication of the source codes by the author with the aim of “protecting honor and dignity”. Another common feature is the “minimalistic” design of both Trojans: NukeBot could only embed web-based injections into the browser, while DiscordiaMiner can download and run files from a remote server. But we cannot say whether these two bots have any more specific connections.
MD5
00B35FB5C534DEA3EA13C8BE4E4585CC
083FD078FECFE156B17A50F73666B43E
0AB8E9C539554CBA532DFC5BC5E10F77
377B9C329EBF7ACFE7DABA55A0E90E98
48E6714A486B67D237B07A7CF586B765
4BD80738059B5D34837633692F18EA08
4E79B826AE4EC544481784EF77E05DE4
4EF5A04A56004AA93167F31296CCACF7
539B092C176183EDCA6A69421B62BCE8
5F8E4CF0971B543525CA807B6A2EC73F
65CF0CC192E69EA54373758C130A983F
7F65252701C80F8D4C1484EE06597DF0
80B04BBC2F18E3FE4625C3E060DA5465
CryptoShuffler
It’s extremely rare for authors of mining software to become fabulously wealthy. With a few exceptions, the wallets used by attackers contain a total of $50-100, received from all incoming transfers during the entire period of the Trojan’s work. However, there are those that do not go down the beaten path, and benefit from “alternative” ways. The authors of the CryptoShuffler Trojan belong in this category.
Kaspersky Lab products detect this Trojan as Trojan-Banker.Win32.CryptoShuffler.gen. MD5 of the file in question is 0ad946c351af8b53eac06c9b8526f8e4
The key feature of CryptoShuffler is the following: instead of wasting processor time on mining, the Trojan simply substitutes the sender’s address in the clipboard! That was once the case with WebMoney and Bitcoin, but this malware sample is aimed at all popular cryptocurrencies.
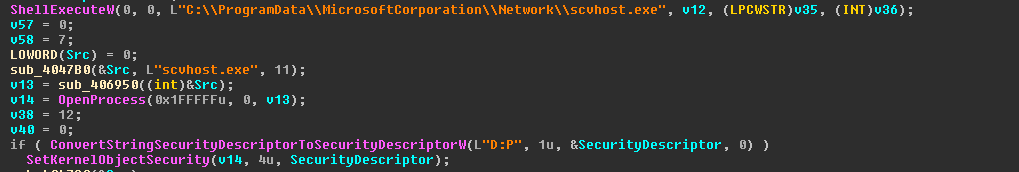
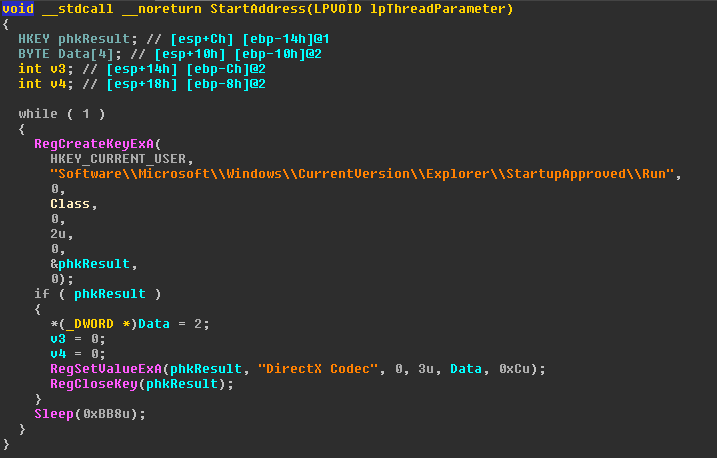
As usually happens in the beginning, the Trojan writes itself into the registry for autoloading.
In later versions of the Trojan, this procedure is slightly different – if the module is implemented as a dynamically loaded library, its further run at the start is performed using the rundll32 system utility. The name of the called procedure and, concurrently, the main function of the represented library is call_directx_9.
The Trojan creates a thread of execution, in which it maintains unchanged the autorun branch specified in the screenshot above.
The substitution itself is performed using the API binding functions OpenClipboard \ GetClipboardData \ SetClipboardData
The search for the corresponding wallet in the string received from the clipboard is performed using regular expressions. Most popular cryptocurrency wallets have a fixed constant at the beginning of the string and a certain length – it is easy to create regular expressions for them. For example, the address of Bitcoin-wallets can be easily recognized by the digit “1” or “3” at the beginning of the string.
The body of the Trojan stores the wallets, corresponding to the specified cryptocurrencies. The main list looks like this.
| WALLET | Currency name |
| 1v9UCfygQf3toN1vA5xyr7LhKmv9QWcwZ | BITCOIN |
| D7uMywpgSyvy9J2RkyQ2oozT4xTmSSWGgR | DOGECOIN |
| LeHrMiPzEUtJen73T5P1bVG2tG8PerzFR1 | LITECOIN |
| Xv4M3y36iu6Fc5ikk8XuQBDFMtRz2xFXKm | DASH |
| 0xfb25b3d5ae0d6866da17c4de253ce439b71d0903 | ETHEREUM |
| 4ZFYNck6mZfG52RMdWThJEXq4Sjdszf719 | MONERO |
| N6VeTbNiFG1oapzPZmeLLkkNC55FQGMTgr | ??? |
| t1VVkuasB7pNHPES2ei6LCqP1hZWb5rfPrB | ZCASH |
| PM44dh7LNEjThgmscw8t5rb9LZqEPc2Upg | ??? |
The biggest profit reaches the cybercriminals’ pockets from the users of Bitcoin wallets – at the time of writing, there were ~ 23 BTC on the balance of their wallet, which at the end of October amounted to approximately $140,000. The amounts in the remaining wallets range from tens to thousands of US dollars.
The malware described is a perfect example of a “rational” gain. The scheme of its operation is simple and effective: no access to pools, no network interaction, and no suspicious processor load.
MD5
095536CA531AE11A218789CF297E71ED
14461D5EA29B26BB88ABF79A36C1E449
1A05F51212DEA00C15B61E9C7B7E647B
1E785429526CC2621BAF8BB05ED17D86
2028383D63244013AA2F9366211E8682
25BF6A132AAE35A9D99E23794A41765F
39569EF2C295D1392C3BC53E70BCF158
50E52DBF0E78FCDDBC42657ED0661A3E
6EB7202BB156E6D90D4931054F9E3439
7AE273CD2243C4AFCC52FDA6BF1C2833
7EC256D0470B0755C952DB122C6BDD0B
80DF8640893E2D7CCD6F66FFF6216016
AA46F95F25C764A96F0FB3C75E1159F8
B7ADC8699CDC02D0AB2D1BB8BE1847F4
D45B0A257F8A0710C7B27980DE22616E
D9A2CD869152F24B1A5294A1C82B7E85
Tales from the blockchain




































robert vendryes
i am trying to remove cryptoshuffler. see referance below
https://www.reddit.com/answers/560d2e33-4658-4159-9313-0a24a906603c?q=how%20to%20remove%20cryptoshuffler
i ran it a few times.. nothing found.
can you comment if your applocation can help me. please advise if your app can help me
Securelist
Hi Robert,
If you suspect that your device is infected with malware, try using Kaspersky to find and remove it. You can also contact our support team to solve the problem if it appears to be tricky: https://support.kaspersky.com/b2c/