
Right after the Venezuelan presidential elections cybercriminals launched a new credential stealing malware joined by a social engineering campaign saying that supposedly the last election was a fraud. The name of the malicious file is “listas-fraude-electoral.pdf.exe” which is translates to “Fraud elections lists” and it spread via a fake Globovision Venezuelan news TV station.
The mentioned malware is quite simple and it sets out to disable the UAC system, which allows the criminals to run administrative commands under restricted users accounts.
C:WindowsSystem32reg.exe ADD HKLMSOFTWAREMicrosoftWindowsCurrentVersionPoliciesSystem /v EnableLUA /t REG_DWORD /d 0 /f
Another action it takes is to redirect DNS requests from the infected machines to 5 different Venezuelan banks to a malicious host that allows it to steal online banking credentials.
One of the interesting aspects of this malware is that it also steals credentials from a Venezuelan Government employees Web site called “Comision de Administracion de Divisas” (The Commission of Currency Administration). www.cadivi.gob.ve
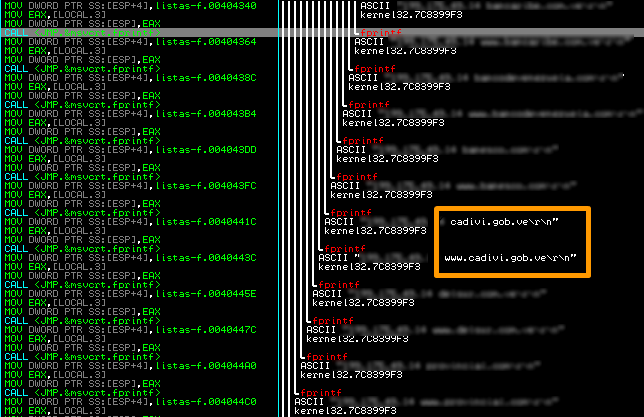
This is an interesting “feature” because it’s strictly related to Venezuelan history. In 2003 the Government of Venezuela decided to create a special commission called CADIVI in order to prevent currency leaks from the country. Nowadays a Venezuelan citizen when travelling abroad has to ask for an authorized amount of currency he/she can spend out of the country. This number is limited to a series of regulations and specific rules such as the number of days that will be spent in a foreign country, the destination and so on. The mentioned commission fixes the final amount in each particular case.
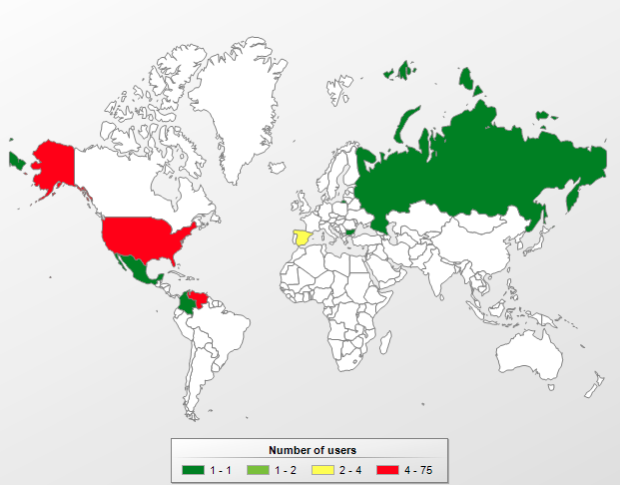
Being that this malware is quite simple and also targeting only Venezuelan banks and CADIVI, we can strongly assume that the cybercriminals who produced it are from Venezuela too. Kaspersky Antivirus detects this threat as Trojan.Win32.Agent.uael and the current infections map looks like this:
The current VirusTotal detection is 17 from 44 anti-virus engines.
Thanks to my mate Kurt for providing the sample.






















Stealing Currency Permits from the Government