
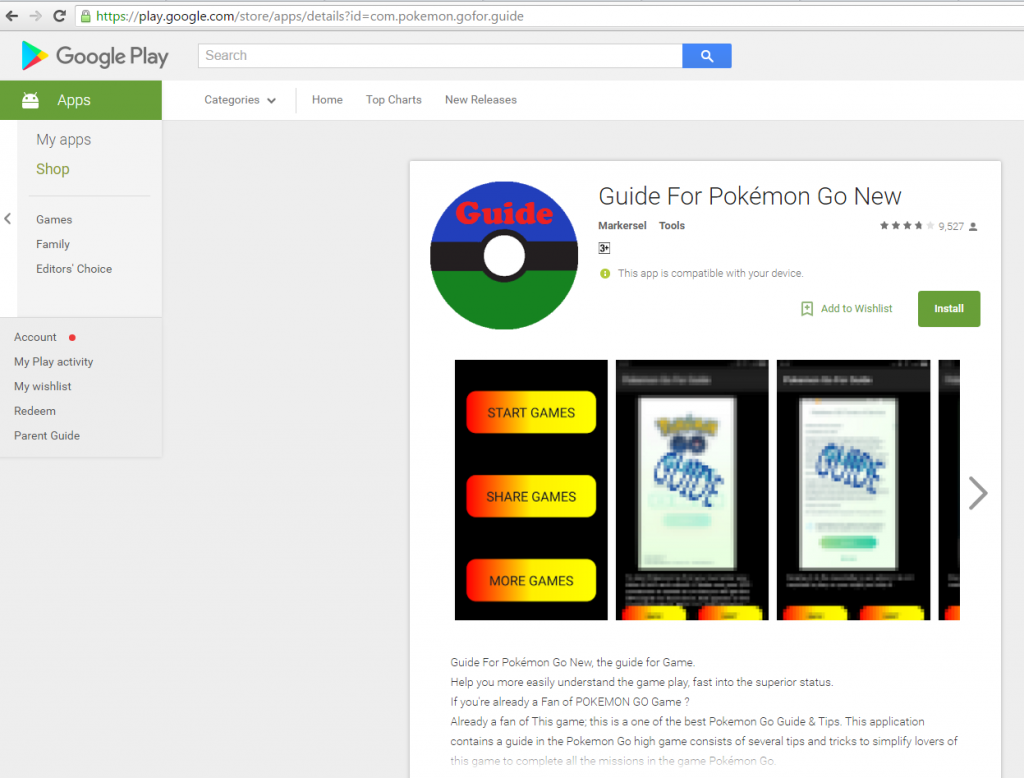
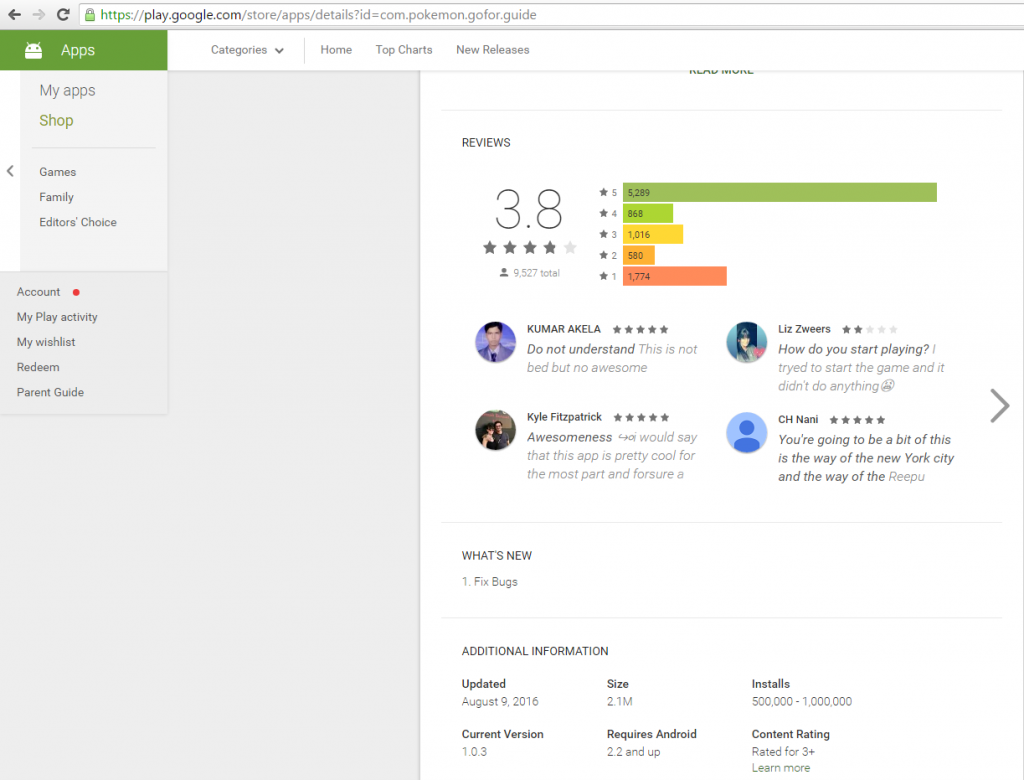
A few days ago we reported to Google the existence of a new malicious app in the Google Play Store. The Trojan presented itself as the “Guide for Pokémon Go”. According to the Google Play Store it has been downloaded more than 500,000 times. Our data suggests there have been at least 6,000 successful infections, including in Russia, India and Indonesia. However, since the app is oriented towards English-speaking users, people in such geographies, and more, are also likely to have been hit.
Analysis reveals that the app contains a malicious piece of code that downloads rooting malware – malware capable of gaining access to the core Android operating system, in this case for the purposes of unsolicited app install and adware.
Kaspersky Lab products detect the Trojan as HEUR:Trojan.AndroidOS.Ztorg.ad.
At least one other version of this particular app was available through Google Play in July 2016. Further, we have tracked back at least nine other apps infected with this Trojan and available on Google Play Store at different times since December 2015.
Trojan characteristics
The Trojan has many layers of defense in place to help it bypass detection. This includes a commercial packer that decrypts the original executable file to make it harder to analyze. The unpacked executable file contains useful code related to the malicious Pokémon Go guide, and one small and obfuscated module.
Process of infection
This small module doesn’t start when the user launches the app. Instead, it waits for the user to install or uninstall another app, then checks to see if that app runs on a real device or on a virtual machine. If it turns out that it’s dealing with a device, the Trojan will wait for a further two hours before starting its malicious activity.
The first thing it does is connect to its command-and-control (CnC) server and upload data about the device, including country, language, device model and OS version.
If the server wants the Trojan to continue it will respond with an ID string. Only if the Trojan receives this ID string will it make its next request to the CnC. If it doesn’t receive anything, it will wait for two hours and then resubmit the first request. This feature is included so that the control server can stop the attack from proceeding if it wants to – skipping those users it does not wish to target, or those which it suspects are a sandbox/virtual machine, for example. Among other things, this provides an additional layer of protection for the malware.
Upon receiving the second request, the CnC server will send the Trojan a JSON file containing a URL. The Trojan downloads file from the specified URL, decrypts it and executes. In our case the Trojan downloaded a file detected as HEUR:Trojan.AndroidOS.Ztorg.a. This file is obfuscated too.
After execution, the Trojan will drop and download some more files. All downloaded files are encrypted and most of them are local root exploit packs for vulnerabilities dating from 2012 to 2015, including one that was previously used by Hacking Team.
These other files represent additional modules of the Trojan and are detected by Kaspersky Lab as:
HEUR:Backdoor.AndroidOS.Ztorg.c, HEUR:Trojan.AndroidOS.Muetan.b, HEUR:Trojan.AndroidOS.Ztorg.ad, HEUR:Backdoor.AndroidOS.Ztorg.h, HEUR:Backdoor.AndroidOS.Ztorg.j, HEUR:Trojan-Dropper.AndroidOS.Agent.cv, HEUR:Trojan.AndroidOS.Hiddad.c. And a few clean tools like busybox and chattr.
Using these exploit packs the Trojan will gain root access rights to the device. After gaining root access, the Trojan will install its modules into the system folders, silently installing and uninstalling other apps and displaying unsolicited ads to the user.
Most of the other apps with this Trojan module available in Google Play had about 10,000 downloads (according to Google Play), but one – “Digital Clock” had more than 100,000 downloads.
MD5 of Malicious Files Mentioned in Article
8CB3A269E50CA1F9E958F685AE4A073C
0235CE101595DD0C594D0117BB64C8C3
Rooting Pokémons in Google Play Store






















Arkadiy
Please explain how can an android application receive a rooting access priviledge?
Mikhail Romaneev
I’ve downloaded sample for 8CB3A269E50CA1F9E958F685AE4A073C . So there is no MainActivity there and NativeActivity, but malware is working on my Android emulator. Could you please say something about technique that it uses to start the app ? Because I don’t see MainActivity class when I decompile it with apktool. And there is no such class in DEX file.
Romero Rodriguez
The malware is packed, so what you seeing in the root dex is just a stub that decrypts original dex and loads it in the memory.
Mikhail Romaneev
Thank you very much, I’ve already found that. But I appreciate you help. That’s cool when guys from all over the world can help each other to analyze malware or some other programming stuff =)
ManjitSingh
Someone I asked my personal information my old personal detail on my old Gmail account to my old Samsung account my Google Drive date on my google photos I have received is I have to someone use without my permission or my order data you can help me please protect myself protect my device
Sandhya
Super