
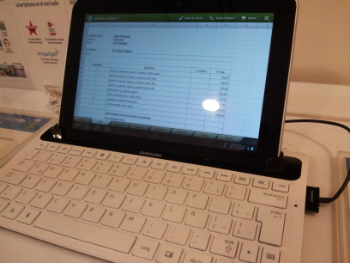
“Forgetting” or “underestimating” are the main reasons for data loss around the world. In an airport lounge during my last trip I came across some cool tab devices running on Android integrated with an external keyboard available for public use and connected to the Internet.
As in the past I performed a quick check of downloaded files, most visited sites and browser history and found a huge list of sensitive information. Here are some examples:
- Access via OWA to a corporate email of a Latin American bank.
- Medical files from Spanish hospitals.
- Commercial offers with personal banking information of a service provider.
- Personal traveller information with full names, IDs, frequent flyer number and the destination of the flight.
- Audit control released by a Latin American government to local companies.
I didn’t check if the browser function “save passwords” was enabled. Just imagine if it was! I also didn’t check the saved cookies. Anyway enough sensitive information was already exposed out there.
Lots of people are not very good at safeguarding their personal information on standard PCs; they are even worse when it comes to tab computers. More often than not, they just don’t know where a file was downloaded on a tab, and they have no idea how to delete it afterwards.
I wonder how much sensitive information is already exposed in this way at airports around the globe! Without any doubt it’s a huge advantage for cybercriminals who know how to use social engineering and a big pain for security officers of the companies who have to train employees. Another important point is when people fly on business – they are usually managers, so any leaked information can compromise not only their personal identity but also a company’s secrets.






















Public points of data loss