
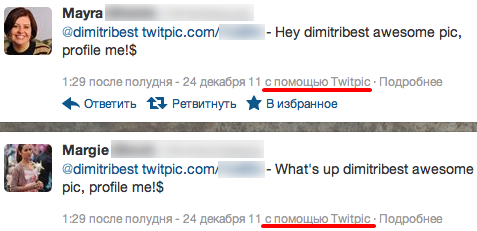
There is a bot activity in Twitter and at the moment is related to the new followers gaining only. What is happening is “profile me” bot is exploring all Twitpic hosted pictures replying to the authors with the same text phrase:
The bot started working on Friday, Dec 23 at 9 pm (GMT -05:00) with the highest peak on Saturday, 3 am the same GMT zone with 0.19% of all Twitter traffic.
In spite of the bot being used to gain followers and to promote porno content via bio user information, potentially it could be used
for any other malicious purpose – like malware spreading via adding additional short URLs to the twits.
We’re monitoring it.





















“Profile me” bot on Twitter