
We’re still monitoring Pegel, and we’ve come across something which piqued our interest: redirects to malicious websites hosting exploits weren’t only coming from infected legitimate sites, but also from flash ads on legitimate sites. Not really standard, so we decided to take a closer look.
The browser displays flash ads which are used in this way just like a normal banner, and if you click, you do end up on an advertising site.
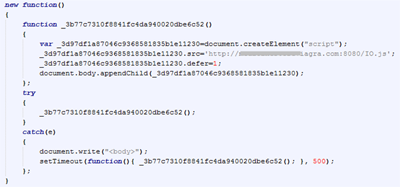
But when we analyzed the ActionScript code of the ad, we found the following script which runs when the ad is loaded:
So when the banner’s displayed, a script on the cybercriminals’ server is run, and it’s this script that redirects the user to a web page hosting exploits.
It looks as though the static banners had been replaced with a very specific type of flash ad. Only one question remained: how was this done?
As it turned out, all the websites which got infected in this way have OpenX, a banner platform, installed. A new OpenX module was released in December last year: Open Flash Chart 2. This module contains a vulnerability (which was identified in the beta version) that makes it possible for cybercriminals to upload executable code to a server.
It seems that the developers of OpenX didn’t know about the vulnerability. Consequently, a vulnerable version of the module was made available for download, and a lot of resources (such as thepiratebay.org, esarcasm.com and tutu.ru) which use OpenX and the vulnerable module ended up infected.
The cybercriminals have tried to ensure that OpenX users can’t update to the most recent version of the product (which has fixed the vulnerability) and they’ve DDoSed openx.org. At the time of writing, the website was still down; however, the link to the new distributive is working, so you can download the new package from here.
If you’ve got OpenX installed, then either update to the new version, or temporarily delete the file admin/plugins/videoReport/lib/ofc2/ofc_upload_image.php from the directory where OpenX is installed.




















Pegel now in banners