
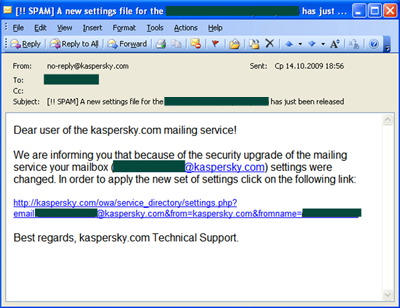
Yesterday we saw a phishing attack targeting users of Outlook Web Access (OWA) service – used worldwide to access email from Microsoft Exchange Servers via the Internet. Users received emails which told them that a security upgrade required them to apply new settings by clicking on the enclosed link.
This is a typical phishing text, but the criminal used domain spoofing to make the email seem as if it came from the recipient’s own domain. In reality, by clicking on the link victims landed on a phishing page which only looked like a standard OWA page.
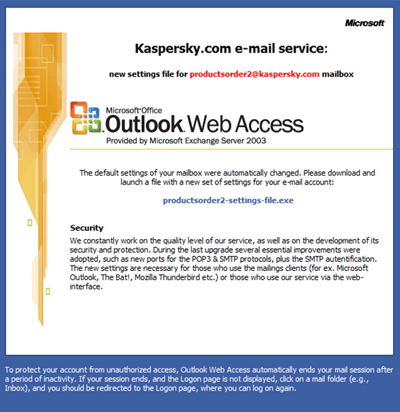
Once on the phishing page, the user was asked to download an .exe file in order to update security settings. Instead of security updates, the victims were installing a Zbot Trojan (Trojan-Spy.Win32.Zbot family).
Interestingly enough, all of the phishing domains were in the .eu and .co.uk zones – which is actually a rare case, since most phisher domains are located in Third World countries.
OWA is a popular service in the business community today so the phishers are likely to reach significant numbers of people. Once again, we remind people to check emails carefully before clicking on links – and recommend network admins to warn their users about this attack.


















OWA Phish – a new vector