
Cybercriminals around the world have already started to point their guns and attacks at the new gTLDs, the ‘generic Top Level Domains’ approved by ICANN and offered by registrars to people interested in buying a new domain name. Recently we found malicious activities including malware and phishing pages registered in the top level domains .club, .berlin, .blue, .computer, .camera, .futbol, .link, .pink, .report, .travel, .vacations and .xyz.
The new gTDLS were recently approved by ICANN and registrars are already offering them as a solution to those bored with the traditional .com or .org and who want more possibilities when registering internet domains. You should be prepared to see websites like”funny.dance“or “joe.dentist“or even “my.creditcard“.
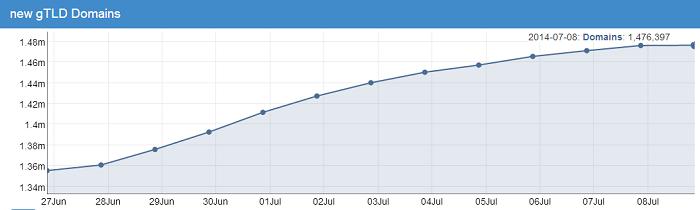
According nTLDStats.com, more than 1.4 million domains have already been registered using these new gTLDs:
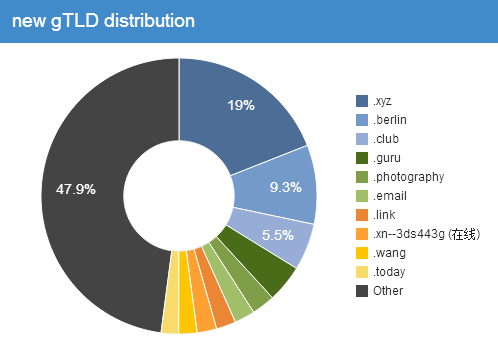
There are now more than 322 new top level domains granted by ICANN, among these the most popular are .xyz (designated at Feb. 2014), .berlin and .club (both designated in January 2014):
Brazilian phishers and domains squatters are particularly interested in these new gTLDs, already having registered several new domains using names of local brands such as banks, online stores, and credit card companies. For example:
- cielo-seucartaobateumbolao.xyz
- megasaldao-americanas.xyz
- lojadoricardoeletro.xyz
- hsbc.club
- santander.club
- bradesco.club
- ricardoeletro.club
- ricardoeletro.computer
- ricardoeletro.camera
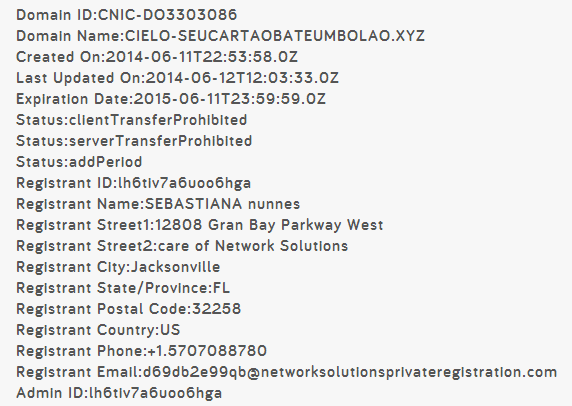
These domains were registered with the intention of being used for phishing campaigns, so it comes as no surprise that the data registered in the respective “whois” databases is completely fake:
Malware is also involved. We’re aware of bad guys hosting their exploit kits in such domains – the Nuclear Exploit Pack is currently using the .blue, .pink, .futbol, and .report gTLDs, as pointed out by security researcher Frank Denis.
But Brazilian bad guys aren’t the only ones interested in the new gTLDs as English-speakers have showcased similar interests by already starting a fraudulent domain that sells coins for online games such as Fifa ’14 and others.
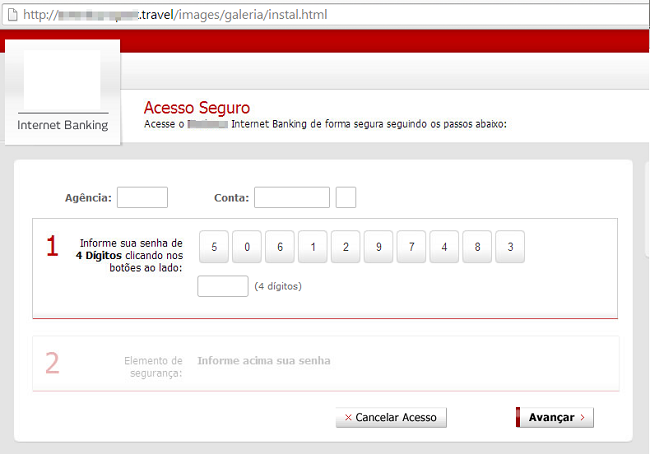
Other phishers already started their phishing campaigns, even using older TLDs such as .travel (started in 2005). As you can see in the following abused domain that hosts a phishing page aimed at a Brazilian bank:
If you’re a regular user, be aware of such links appearing in email messages or in social networks – they can be just as dangerous as others links. If you’re a company, it’s a great idea to start a brand monitoring process to insure that your company name or brand aren’t being used in campaigns involving these new TLDs.
Kaspersky users are protected against all of these attacks.























New gTLDs, same attacks