
Yesterday it was the Haiti Earthquake, Alberto Gonzalez or any other trendy topic and today cyber criminals are using the Moscow bombing. The aim is the same – to infect as more people as it’s possible.
The criminals base their targets on the trend topics. Right now Twitter has the next topics as the most looked for by people:
#imfromTeam
#nowplaying
#musicmonday
#idoit2
Easter
Justin Bieber
Moscow
#MM
#TLS
I ♥
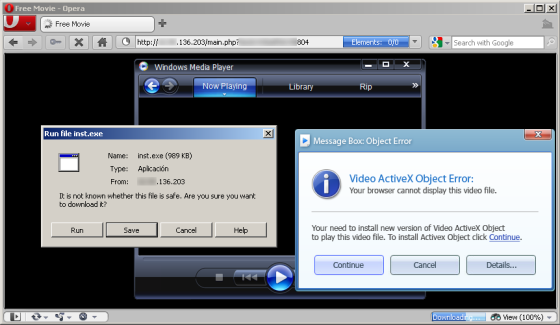
Today the most exploited topic to infect people is ‘Moscow’. Please, be careful since the criminals have a lot of automatically created fake Twitter profiles spreading fake news about this subject and leading to malware:
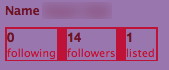
The bad news seems like the criminals are having success. I checked some of malicious Twitter profiles and found they already have legitimate followers. That means that people/users didn’t suspect the news was fake and probably got infected.
This is an example of a malicious Twitter criminals profiles having 14 legitimate not malicious followers:
Please, be careful. Don’t click in all and any clicks, specially when it’s a Trend Topic. There is a high probability of getting infected.
Kaspersky Ant-Virus detects the threat by our proactive technologies as PDM.Trojan.Generic The overall VirusTotal detection of that particular malicious samples is 9/42 (21.43%)





















Moscow bombings lead to Twitter malware ‘bombings’