
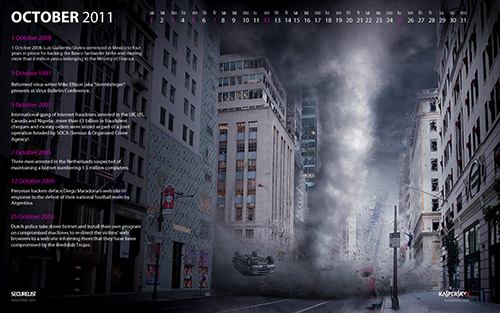
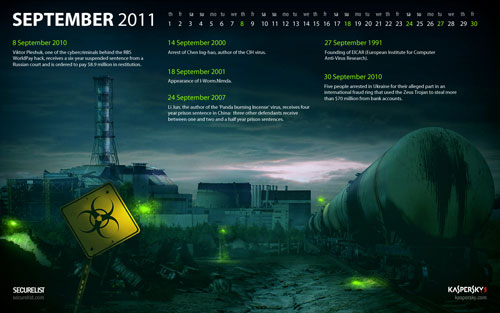
Here’s the latest of our malware calendar wallpapers.

1280×800 | 1680×1050 | 1920×1200 | 2560×1600
Christmas brings many more people online since the Internet provides a quick and convenient way to buy Christmas gifts. This makes it the perfect time for cybercriminals to cash-in on online activity. So it’s also a good time for a reminder about the basic things you can do to reduce the risk of cybercriminals spoiling your Christmas.
- Install Internet security software and keep it updated.
- Keep Windows and other applications up-to-date.
- Backup your data regularly to a CD, DVD, or external USB drive.
- Don’t respond to email messages if you don’t know the sender.
- Don’t click on email attachments if you don’t know the sender.
- Don’t click on links in email or IM (instant messaging) messages. Type the address directly into your web browser.
- Don’t give out personal information in response to an email or other message, even if it looks official.
- Only shop, bank or socialise on secure sites. Make sure the URL starts with ‘https://’.
- Use a different password for each web site or service you use. Don’t recycle them (e.g. ‘jackie1’, ‘jackie2’). Don’t make them easy to guess (e.g. mum’s name, pet’s name). Don’t tell anyone your passwords.



















Malware Calendar Wallpaper for December 2011