
Today while conducting research on the alleged Latvian power hack, I came across some interesting malvertising on imageshack, where pictures of the purported hack have been hosted.
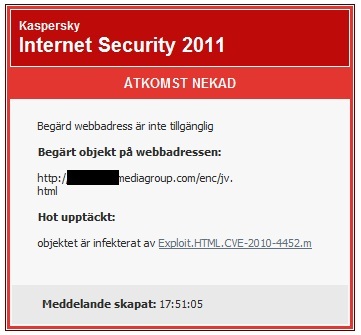
Advertising on the page loads a exploitable Java vulnerability that Kaspersky recognizes as Exploit.HTML.CVE.2010-4452.m, which then tries to download Trojan.win32.TDSS.cgir. TDSS as some of you may recognize is a rootkit that can access Windows at its lowest levels and can prove extremely difficult to remove.
Upon opening the page, the advertisement loads, and a connection to http://–removed–ediagroup.com/enc/jv.html is made. This launches the actual exploit. A second page http://–removed–ediagroup.com/load.php?2 is loaded which drops the Trojan containing the TDSS malware.
Kaspersky already detects both the exploit, as well as the Trojan payload. This serves as a reminder of the importance of keeping your Anti-virus up to date.
We will update with further details as they become available.




















Malvertising on ImageShack