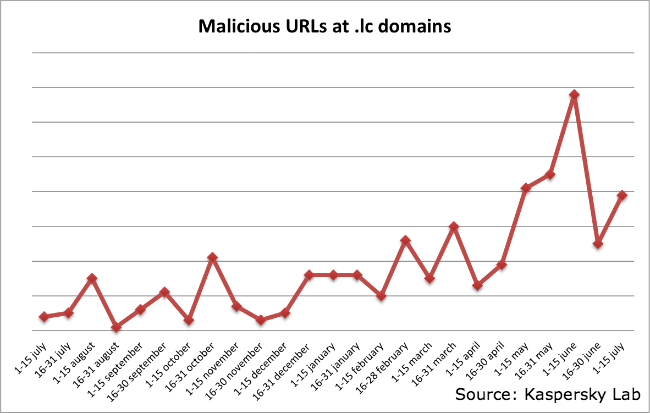
While analyzing suspicious URLs I found out that more and more malicious URLs are coming from.lc domain, which formally belongs to Santa Lucia country located in in the eastern Caribbean Sea.
Our statistics confirm this trend.
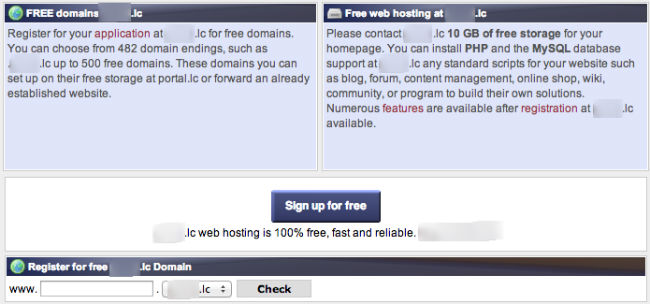
Cybercriminals from different places of the world are actively using this domain, including cybercriminals from Brazil abusing free Web hosting available in that country.
How many legitimate domains at .lc zone have you ever had to visit in your life? If the answer is zero, so maybe it’s time to start filtering access to this domain, especially on the corporate Firewall / Proxy layer.
Follow me @dimitribest
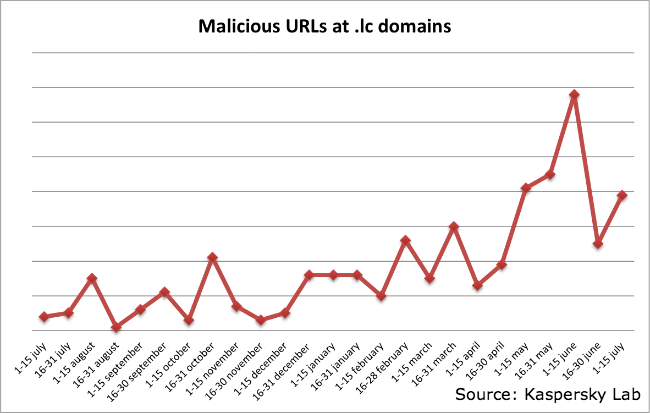





















Malicious URLs in .lc Zone