
The story of a researcher who wanted to see how vulnerable he actually was
Introduction
Very often new terms get over-hyped in the IT security industry. At the moment we can find articles about how hackers and researchers find vulnerabilities in for example cars, refrigerators, hotels or home alarm systems. All of these things go under the term IoT (Internet of Things), and it’s one of the most hyped topics in the industry. The only problem with this kind of research is that we cannot really relate to it all: it’s pretty cool, detailed research, but if you as a reader cannot relate to the attacks, the research is not understood in the proper way.
We often try to predict the future with proactive research, and I think it can be important to try to predict the future and conduct proactive security research. But I think it’s even more important to talk about what’s relevant, and talk about threats that people can relate to. I started to think about this topic, and figured that if we can’t secure ourselves against current threats, what good will it do to identify potential new future threats?
Threats are around us right now, while you’re reading this document. As users in a connected digital environment we need to ask ourselves; ‘What’s the current threat level?’ and ‘How vulnerable am I?’ – Especially when we start building small home office networks. A typical modern home can have around five devices connected to the local network which aren’t computers, tablets or cellphones. I’m talking about devices such as a smart TV, printer, game console, network storage device and some kind of media player/satellite receiver.
I decided to start a research project and conduct research which I thought was relevant, trying to identify how easy it would be to hack my own home. Are the devices connected to my network vulnerable? What could an attacker actually do if these devices were compromised? Is my home ‘hackable?’. Before I started my research I was pretty sure that my home was pretty secure; I mean, I’ve been working in the security industry for over 15 years, and I’m quite paranoid when it comes to applying security patches, etc. I reckoned there must be other homes that are much more hackable than mine, because I don’t really have a lot of ‘hi-tech’ kit at home.
During my research I didn’t focus on computers, tablets or cellphones, but rather on all the other devices I have connected to my network at home. To my surprise it turns out that I actually have quite a lot of different things connected to my network. Most of them were home entertainment devices: smart TV, satellite receiver, DVD/Blu-ray player, network storage devices and gaming consoles. I’m also at the moment relocating to a new house, and I’ve been talking with my local security company. They’re suggesting I get the latest alarm system, which connects to the network and can be controlled with my mobile device… After this research, I’m not so sure it’s a good idea.
Some of the devices on my network were for example:
- Network-attached storage (NAS) from famous vendor #1
- NAS from famous vendor #2
- Smart TV
- Satellite receiver
- Router from my ISP
- Printer
Before conducting the research I had all devices update with the latest firmware version. During this process I also noticed that not all devices had automated update checks, which made the entire process quite tedious. As a consumer I had to manually download and install the new firmware on some of the devices, which was actually not that simple because the new firmware files were not that easy to find, and the entire update process wasn’t very suitable for a normal computer user. Another interesting observation was that most of the products were discontinued more than a year back or simply didn’t even have any updates available. This got me thinking… do these home business and entertainment products only ‘live’ for about a year before they get discontinued?
The goal
So what am I trying to prove with this research? Let me explain why I think this is important research. When I started this project I soon noticed that I could take several different approaches to the research, but for me the main goal I wanted to achieve was to see how vulnerable our homes really are, and also identify real, practical and relevant attack vectors to prove just that.
In general we’re quite good at protecting our endpoints and use security software to help us do so. We also become aware from newspapers and blogs about how to raise our security level. Most people today know what a computer virus is, that we should have strong passwords, and that it’s important to install the latest security patches; but do we really think about all aspects? It’s quite common for a security researcher to talk about a locked door on a glass house, and I wanted to have a similar approach with this research. I wanted to demonstrate that even with an IT-security mindset we focus on protecting our endpoints, and tend to forget that there are other devices connected to our networks. We want to prevent people hacking or infecting our computers because we don’t want our data to be stolen, but we then go home and do a full backup of our data to a device that’s even more vulnerable than our computer.
The audience for this research is not only consumers but also companies. We need to understand that EVERYTHING we connect to the network might be a stepping stone for an attacker, or may even become an attacker’s invisible ‘base’ that he/she will use to regain access to your network after its been compromised. Just imagine a scenario where you notice you’ve been compromised, you do everything in the book to bring it back to normal again, you backup your data, re-install your devices and make sure that the new installation is protected against malicious code and all updates are installed; but then six months later you get compromised again, and all your new data is stolen again… How would that even be possible?
The attacker might have compromised your network storage device and turned it into a backdoor. The malicious software is undetected because there’s no protection against malicious code running on that device, and the malicious software cannot be deleted because you don’t have permission to access the file system on the device; not even a factory reset would solve the problem. Or it might be that the attacker actually used your compromised smart TV to regain network access to your corporate network, since the TV is connected to the same network as your employees, and there are no network restrictions for the smart TV.
The goal with my research was to try to be the baddie, to use my home entertainment devices for malicious intentions, to actually compromise them and use them as either stepping stones to launch further attacks or as a backdoor in my own network.
What I did not try to do in this report is bash or criticize any vendor; the devices that were tested during this research were my own personal devices, and that’s the reason those devices were chosen for this project. All vulnerabilities have been reported to the respective vendors, and they’re working on solutions for these products. I will not disclose all the vulnerabilities that were identified in this research or any technical details about the vulnerabilities because that will only help the bad guys. If you want further technical details regarding the research project feel free to contact us.
The impact
So, I had all these different devices connected to my network, but where was I to I start? I decided to begin by defining the different attack scenarios I would include in my research rather than just attacking these devices without any criteria. One or all of the following criteria had to be achieved to consider the test successful:
- To obtain access to the device; for example, to get access to files on the network storage devices;
- To obtain administrative access to the device, not just in the administrative interface, but also at the OS level;
- To be able to transform/modify the device for my personal interest (backdoor, stepping stone, etc.).
There are probably loads of other scenarios that could be useful to test, but my time was limited and I simply needed to prove a point. I started out by just fooling around with the web interfaces for the different devices and to my surprise it didn’t take long before I had found remotely exploitable command execution vulnerabilities with full administrative permissions at the OS level on both network storage devices.
At this point I asked myself, ‘is it really that easy?’ I then thought about the two newly discovered vulnerabilities and realized both were in the administrative interface after authenticating as the administrative user. I needed to have the same preconditions as the attacker. So I tried to find vulnerabilities without using any of my access credentials. At this point it was a little bit harder, but after some poking around I found the main configuration file – it was available remotely to any user on the network. In the configuration file all the password hashes were stored, which made it real easy to obtain the administrative interface again and then use the vulnerabilities I found before to execute system commands on the device.
After further poking around I found more vulnerabilities, which could also be exploited without authentication to execute system commands as root (highest privileges) on the device. At this point it was more or less game over for both of the network storage devices; I didn’t just have access to the entire file system of the devices, it was also very easy for me to infect the devices with some Trojan or backdoor that would turn the devices into zombies in a botnet – or give the attacker a backdoor to, for example, carry out further attacks from the device.
Both compromised devices where running a Linux 2.6.x kernel, and a lot of interpreters such as perl and python. One of them also had the GNU C compiler installed, which would make the attackers’ life much easier. Since one of my attack scenarios was to transform the compromised device into a backdoor, I simply used one of the public IRC bots as my test case. Within seconds I had turned my network storage device into a zombie in a botnet.
This was extremely easy because the compromised network storage device is used to store files, so I could simply upload my malicious file and place it outside the shared folders somewhere else on the file system, which results in the owner of the device not being able to delete the file without using the same vulnerabilities we used to both upload and execute our IRC Trojan.
After researching the network storage devices I found over 14 vulnerabilities that would allow an attacker to remotely be able to execute system commands with the highest administrative privileges. The two devices did not just have a vulnerable web interface, but the local security on the devices was also very poor. The devices had very weak passwords, a lot of configuration files had incorrect permissions, and they also contained passwords in clear text.
To give you another example on how bad the local security was, I can tell you that on one of the storage devices the administrative root password was ‘1’. I do understand that these devices are not built with Fort Knox security in mind, but to have a one character-long password is against all reasonable rules.
Due to the poor security, and the fact that I had access to the file system, it was also very simple to identify several scripts which enabled features in the device that weren’t documented anywhere. Functions which allowed an external user to enable services and other interesting things on the devices such as remote admin interfaces (telnetd, sshd). I might write more about these ‘hidden’ features in a different post because I need to conduct deeper research regarding these files.
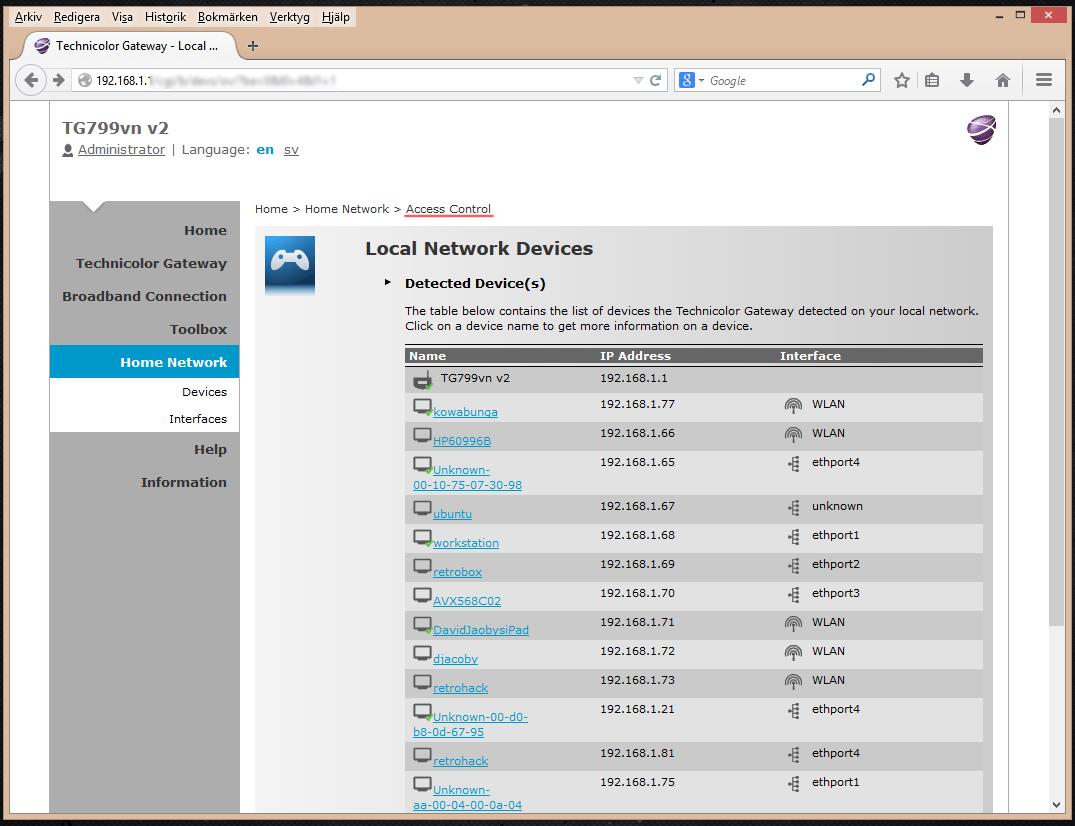
During the research project I stumbled upon some other devices that had ‘hidden’ features; one of those devices was my DSL router which was provided by my ISP. After I logged in using the admin credentials I received from the ISP I could navigate around the web interface. The interface was pretty simple to use, and I quickly noticed how the URL changed when I navigated through the menu. Each function in the menu was assigned a number; the first function in the menu had the numeral 0, and then it incremented with one for each option. The interesting thing was that sometimes a function jumped to an unexpected number and a few numbers were missed, but when you then entered the missed numbers in the URL address bar you were prompted with a menu option that didn’t exist in the menu list, but the name of that ‘hidden’ function was displayed in the web interface.
I started to brute force these numbers, and found that there were tons of functions I didn’t have access to. I just assume that my ISP or the vendor have FULL CONTROL over the device, and can do anything they want with it and access all these functions I don’t have permission to use. By just looking at the ‘hidden’ function names it seems that the ISP can for example create tunnels so as to connect to any device on the network. Just imagine if these functions fell into the hands of the wrong people? I understand that these functions are most likely supposed to be helping the ISP perform support functions, but when you log in using the administrative account you don’t have full control over what you consider is your own device, and thus it becomes quite scary. Especially when some of the names have equally scary names like ‘Web Cameras’, ‘Telephony Expert Configure’, ‘Access Control’, ‘WAN-Sensing’ and ‘Update’.
Below are some screenshots of these hidden functions.
I’m currently still researching these things to see what the functions really do. If I find anything interesting I’m pretty sure there’ll be another blog post.
Meantime, I started to examine the other devices connected to my home network; for example, my Dreambox: it still had the default username and password, which was also the administrative root account on the device! The device runs Linux, which would be an easy target for an attacker. Most of the other devices were pretty secure but an entire audit of these kinds of devices would be difficult because you need to find alternative ways to determine if an attack was successful or not since you don’t have full access to most of the devices.
After a few days of poking around I still hadn’t found anything that would cover the three scenarios – nothing really worth mentioning. The research project was also quite difficult to perform because I was auditing my personal devices, and I didn’t want to break anything. I had naturally paid for all these devices out of my own pocket!
I had to take a different approach and at this point I had to get creative. I had to play with the idea that I’m the attacker, and I’ve already compromised the two network storage devices, and so what can I do next?’ My first thought was to see if I could do something with the media players (smart TV and DVD player) because they’re most likely reading information from the storage devices (which I’d already compromised). At this point I was researching potential code execution vulnerabilities with the smart TV and DVD player, but due to the high price I paid for the devices I wasn’t able to investigate this further. It wasn’t only a question of the wasted money if I were to break my brand new LED smart TV, but also I had no idea of how I would explain my wrecking the telly to the kids; how were they going to watch Scooby Doo?
I decided to stop researching them, and spent some time contacting the different vendors to see if the vulnerabilities were actually exploitable and work together with the vendors to verify these potential security issues. It’s much easier for them to do it since they have access to the source code and can confirm if the vulnerability is valid or not much quicker (and I guess they don’t really care of they break any devices).
At first I had some trouble contacting these vendors because on the websites there’s little useful contact information for the engineers or C-level people who would be able to help me get through to the appropriate people. After some lurking around and asking people in my professional network I was finally able to get in contact with the people I needed and they were very grateful for the information I could share regarding the vulnerabilities and research approaches.
We are now trying to identify if we would be able to transform the smart TV and DVD/Blu-ray player into the same type of stepping stone and backdoor as the compromised storage devices. More information will be shared on this topic later since this research project is ongoing.
I did identify one curious security issue with the smart TV. When the user accesses the main setup menu on the TV, all the thumbnails and widgets get downloaded from the vendor’s servers if the device has network access. The TV didn’t use any kind of authentication or encryption when it was downloading the content, which means that an attacker could perform a man-in-the-middle attack on the TV and modify the images in the administrative interface; the attacker could also have the TV load any JavaScript file, which isn’t a good thing. A potential attack vector is to use JavaScript to read local files from the device, and use the content of the files to find even more vulnerabilities. But this is something I’m working on with the vendor to see if it’s possible or not. As a proof of concept for my attack, I changed the thumbnail of a widget to a picture of everyone’s favorite, Borat. Yakshemash!
Summary
For the most of my life I was a total security junkie, doing everything from working as a penetration tester to a public speaker and adviser for law enforcement agencies. IT security is really one of my biggest passions in life, but for the last few years I seem to have reached a point in my life where I’m actually quite tired of reading the same security bulletins year after year. It’s time we start doing something about the problems, and one thing we can do is start talking about security threats that are relevant, and also in a language that will make everyone understand them. We as security experts need to take more responsibility and talk about threats that are relevant today – threats that affect you and me. We also need to come up with smart and simple suggestions, conclusions and solutions on how to mitigate those threats by using the software and technology that we already have.
I’ve always been fascinated by new vulnerabilities and exploitation techniques, but to be honest, what good does it do only releasing vulnerability information when we’re not making people understand the bigger picture. We think that IT security is all about software vulnerabilities and I know that half of this post is only talking about vulnerabilities, but the goal with this research is not to brag about all the undiscovered vulnerabilities I found, or that there are big security problems in the home entertainment product line. There will always be vulnerabilities, and we need to understand that; however, by understanding I don’t mean accepting. What I mean is that we need to actually do something about it; we need to know what the impact is and assume that our devices can be, or are already, compromised. We need to start assuming that products are vulnerable and that attackers can and will gain access to them.
I would like to conclude this research by saying that we as individuals and also companies need to understand the risks with network devices. We also need to understand that our information is not secure just because we have a strong password or are running some protection against malicious code. We also need to understand that there are so many things that we do not have control over, and that we are largely in the hands of the software and hardware vendors. It took me less than 20 minutes to find and verify extremely serious vulnerabilities in a device considered to be secure – a device we trust and on which we store all the information we don’t want stolen.
I remember when I proposed this research to my boss; he asked me what I thought the outcome would be. I was not developing new security solutions for home entertainment devices; I was only identifying security problems, so the only answer I could give him was that I wanted to conduct this research to make people aware that there is a problem, and that we as individuals need to try and improve our personal security in different ways to how it was done in the past; we need to change our mindset and the whole game!
I would also like to give some feedback to all the vendors out there: we need to come up with a better way to support and secure your products. It’s not really acceptable that a product is considered as discontinued after only 12 months; it’s not okay to have one character passwords; and it’s not okay to think of these devices just as ‘entertainment’ devices. It’s not okay to have a readable configuration file containing all user credentials – especially on a network storage device.
We need to come up with alternative solutions that can help individuals and companies improve their security. This is not a problem you simply can fix by installing a product or security patch; therefore, I would like to end this post by saying that even though the home entertainment industry might not be focused on security, we at KL do, and with just a few simple tips I think we can raise the security level a little bit higher. Hopefully some of the vendors will read this research and improve their software security; but until then, here are some simple tips from my side:
- Make sure all your devices are up to date with all the latest security and firmware updates. This is a problem for a lot of home business and entertainment devices, but it is still the best thing you can do to avoiding being at the mercy of known vulnerabilities. It also gives you an indication of whether the devices have any updates at all to install, or if it’s considered to be a ‘dead’ product.
- Make sure that the default username and password are changed; this is the first thing an attacker will try when attempting to compromise your device. Remember that even if it’s a ‘stupid’ product such as a satellite receiver or a network hard drive, the administrative interfaces are often vulnerable to serious vulnerabilities.
- Use encryption, even on the files you store in your network storage device. If you do not have access to an encryption tool, you can simply put your files in a password-protected ZIP file; it’s still better than not doing anything at all.
- Most home routers and switches have the possibility to set up several different DMZ/VLAN. This means that you can setup your own ‘private’ network for your network devices, which will restrict network access to and from this device.
- Use common sense and understand that everything can be hacked, even your hardware devices.
- If you’re really paranoid you can always monitor the outbound network traffic from these devices to see if there’s anything strange going on, but this does require some technical knowledge. Another good tip is to restrict network devices from accessing sites they’re not supposed to access, and only allow them to pull updates and nothing else.
IoT: How I hacked my home

























R Foreman
You should tell people how you gained access, instead of just saying you mysteriously were able to open the ‘main configuration file.’ Just a suggestion.
David Jacoby
Mr. Foreman,
I cannot disclosure any technical vulnerability information because the affected vendors is working on fixing the vulnerabilities. But i can tell you this, that some of the vulnerabilties, including the “configration file” disclosure one was very simple to exploit. You only had to visit a specific URL on the targeted device, and you could obtain the entire configuration file.
Im sorry i cannot give you more information, but i cannot share these details yet, hopefully soon.
Umo
Like “R Foreman” earlier said – good article but leads nowhere. Everyone knows that there are vulnerabilities in almost every device – sharing how you found them will help the community as a whole. Hope you update the article with steps to test the vulnerabilities.
SBS0518
This article has plenty of useful info in it. Why would Mr. Jacoby provide such details that would show you how to hack other peoples devices. What the article highlights is that vulns exist and that the reader should take the necessary steps to examine their networks and further lock them down.
If you want to know how he did it, do the research for yourself and prove it for yourself….
Zoli
Nice findings!
One thing I don’t understand is the threat model. Almost all exploits identified are on the home network only, which is not directly accessible by the attacker from the internet (in a typical environment these devices are behind NAT). Which means the attacker either has to have access to the home network, or combine the attacks with CSRF, which also presumes that the attacker knows the IP and version of the devices – not realistic. The only realistic scenario I can think of is when the IoT devices are using IPv6.
anon
Zoli, Nat is not a security barrier. Most home routers themselves expose external interfaces that have security holes, have ports opened on them automatically via UPNP or other protocols that are similar (see HD Moore’s work on UPNP vulns), and its easy to gain a foothold on a home user’s laptop and then pivot to their internal network for a more permanent foothold since their vulnerable NAS will probaly be running and not updated for months/years.
The threat scenario is real.
Marco Schuster
Some of these vulnerabilities are exploitable by “raw http”, i.e. load 256 iframes with src=http://192.168.1.x/…
This obviously takes advantage of many people leaving the IP numbering at factory default, which e.g. for AVM Fritz!Boxes is 192.168.178.x and 192.168.x.y for others, x being 0,1 or 2.
Or, even better, do the probing with AJAX and listen for the device response, so you can ping-back a successful infection to the attacker.
Pete
As these vulnerablities seem to be in the web interfaces, it’s rather trivial – any website can execute javascript to scan for these devices in the typical IP ranges; NAT won’t prevent your browser to connect to 192.168.1.100/vulnerableendpoint/xxx (and the same for a thousand other possible address-endpoint combinations); send the results to http://www.badguy.com, retrieve a “package” from http://www.badguy.com and post it to your SmartTV.
David Jacoby
Hi everyone,
Yes, you guys are correct. Most of the found vulnreabilties where located in the web interfcace. Some of the vulnerabilities, including some Remote Command Execution vulns could be triggered before authenticating, and in simple GET requests.
The only trick, which has also been mentioned in the comments is to find the device on the LAN, but most machines are setup to use default ranges, just as Marco said in his comment.
Enno Rey
Zoli,
given pretty much all IoT devices will use IPv6 in the near future, all these _are_ realistic scenarios.
Best
Enno
Ryan
@Zoli
Correct, the most dangerous router vulnerabilities are remotely-triggerable XSS and CSRF attacks, or the occasional wide open remote management panel. However, it is quite realistic for them to work out the IP address; it would only take a few seconds to bruteforce the IP addresses of, I would imagine, 98% or more of consumer routers. 192.168.0.1, .1.1, .2.1, .3.1 … etc.
It’s also still useful to know these kinds of locally exploitable vulnerabilities are out there.
David Jacoby
Hi Zoli,
Well, remember that not everyone understand how to configure their home networks, and put devices accessible over the Internet. Imagine scenarios where an attacker have already compromised an network, and want to install a very persistant backdoor, to do that on a computer or server is not the most convenient, but what if the backdoor was running inside the NAS? Smart TV? or printer?
Your scenario is also very good, with IPv6 when EVERYTHING is connected to the Internet… but the threat model was not the real case in this research. The discussion that vendors in general dont put any effort on making consumer devices security is what i wanted to proove. Just because they are consumer products, doesnt mean that we should ignore the security aspect?
I wanted to proove that to really work with security, we need to look into ALL aspects. Not just password, vulnerability and anti malware management. We have devices in our homes and offices that we do not have ANY control over, and its a nightmare when these devices are vulnerable to very simple, and trivial things and you do not have any real options on how to make them less vulnerable.
randydutton
It gets worse.
When shopping for a garage door opener I found that ALL were Internet ready. They’ve been designed to allow remote checking to see if the door is open or closed. It allows the homeowner to close it remotely.
My LG refrigerator has a microphone and speaker which allows it to talk to a service technician’s computer over a cell or cordless. The owner’s manual says you have to hold the phone to the top left hinge. It’s not WiFi enabled, but no doubt other refrigerators are.
Zunguri
Of course the two types of questions in mind after reading this post are:
1) How did he do …..?
2) What device is that?
Answering the first would set some number of people with more curiosity than knowledge into a campaign of “helping” their neighbors. Answering the second would ruin any business development opportunity with device makers.
A log of all traffic coming through the admin interface would be interesting. With most support people being so well suited for their jobs, I have to wonder how often the use of “hidden” functionality is actually for support.
David Jacoby
You can read about which TYPE of devices, but not the vendor/brand. The brand is not important because the test is just to proove that the devices we put in our homes are inseucre. So im pretty sure other brands are also vulnerable.
David Jacoby
You can read about which TYPE of devices, but not the vendor/brand. The brand is not important because the test is just to proove that the devices we put in our homes are inseucre. So im pretty sure other brands are also vulnerable.
How i did it? Well, i used my browser, telnet, python, perl and netcat to do it 🙂 Noting else…well ok, “Live HTTP headers” extention for Firefox 🙂
K.Vee.Shanker.
Hi David,
It’s very nice of you to have used your home network and exposed their very vulnerable status to the public. Thanks. People yearn for more and more devices on net, but hardly realize that only makes them more and more vulnerable to hacking. ‘More is Merrier’ has to be understood as ‘Merrier to the Hacker’ – I suppose!
Roger
Wow, thanks for making me think guys. One quick thought, so if I get hacked loose money etc, I find that the vendor is at fault, I should be able to sue big time!
Pramod Kumar
Hi David,
Thank you for the time and effort to put up the article. I have a scenario as follows,
A Router with a strong password.
Behind the router, a lap top with strong security and a smart bulb with a weak security..
.What kind of a hack can take place?
People keep saying a weak smart device can blow a hole in the net work. What does this mean? Can the smart device be accessed bypassing the router?
Andrej Zieger
Hey David,
thank you for the great post.
I do some research on IoT Security as well and building some kind of inventory of smart devices and their security measures and/or faults. And hell I guess there are more failures than achievements…
Could you provide me with more details on the devices (specific product or at least the brand)? It is not to blame or disclose it, but more or less to not count problems twice…
You can reach me privately: zieger {a-t} dfn-cert.de
@Pramod Kumar
Well if your security depends on the security of your network, it is only as strong as the weakest element reachable from the outside.
Imaging a “combination of attacks” using multiple vulnerabilities:
– TV downloads from the public and executes javascript (may be limited, but further http requests are possible)
Does not sound bad alone… “uhh maybe an attacker could switch my program”
– Security Hub (including alarm and door lock) has an unsecured web interface
“well my wifi is protected” <– but your tv is not <– "but when I watch TV I am at home…"
– NAS (or a lot other devices as my study shows me) allow unauthenticated code execution through web interface (HTTP / URL)
The whole device can be hijacked. Now it is more than just reading your files…
When combining those vulnerabilities a hacker can first access your TV to execute code on the NAS to implement a point of persistence. Later when your not at home (the hacker knows as your smart bulbs are off / your security cam tells him / your door lock tells him), the hacker accesses the security hub and opens the door as well as disabled alarm and security cameras.
So essentially you compromised your (even physical) security by introducing awesome smart devices into your home.
Oh of course your laptop is still safely protected by your password, right? But do you have HDD encryption? Else with the above steps he will have physical access and can just boot directly into a root shell and read anything he wants to.
Even if you don't have a smart lock, from the point of persistence the hacker can just take his time and scan the security of your laptop. Does an unprotected http server run on some port? Is an sql database listening? ssh? telnet 0o? Or just sniff wireless traffic which might be unencrypted within the wifi. Or just modify a file on your NAS and then persuade you to execute it on your still secure laptop.
You see there are a lot of possibilities, if your are already inside the network…
And if you are thinking about the LIFX smart bulb, this nasty thing just told attackers directly the wifi credentials. Though it is fixed now.
Hope that answers your question – even if it is some time since…
–
Neil Gotschall
Thank you for the ‘Heads Up’ article. I am researching info prior to purchasing a NAS and your article came up in a Google. Thank you. During my research it turns out I haven’t had enough paranoia…yours and other articles are enlightening.
Cheers…
James Sibley
With WebRTC it is pretty easy to determine a victim’s internal network range. And then with CSRF you can spam all /24 addresses with exploits hoping to hit an affected device. An example of this is the WD My Cloud command injection exploit: http://versprite.com/og/command-injection-in-the-wd-my-cloud-nas/