
There’s nothing new in Brazilian cybercriminals exploiting social networks to distribute their malicious code. Orkut was first, followed by Twitter, and now it’s Facebook’s turn.
Facebook is becoming increasingly popular in Brazil and we are witnessing more and more Brazilian bad guys switching their focus to it. We received some proof this weekend: a Brazilian instant message (IM) worm created to steal Facebook passwords and login, and use the infected profile to spread malicious links among Portuguese speakers.
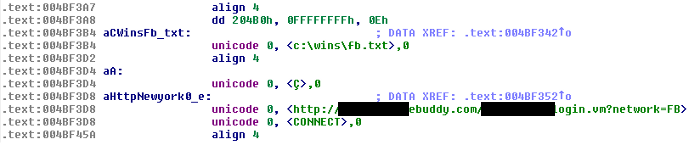
The worm (md5 d8dd66f2ec659687c56feb31ae1ac692) is distributed in a drive-by-download attack. After infecting the user’s machine a malicious applet downloads lots of different files, including the IM worm responsible for stealing users’ Facebook passwords. The worm is designed to connect to the victim profile via the web service Ebuddy.com or via the mobile version of Facebook, and capable of posting the content of the file fb.txt:
The content of the file is a message written in Portuguese, pointing to a malicious domain. The message is sent to other Facebook users via chat:
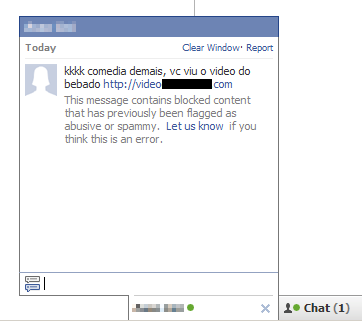
The malicious message in Portuguese says: “It’s really funny, take a look at this video of a drunk”
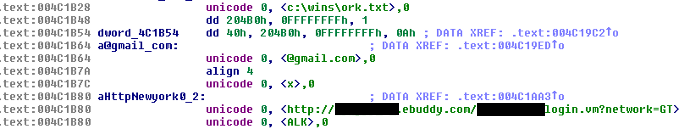
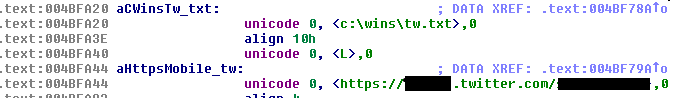
The worm is also capable of sending the same malicious message to other social networks and IM services such as:
GTalk/Orkut:
and Twitter
The worm is not currently widespread. Facebook already blocks the malicious link sent in conversations via chat; most infected users are from Portuguese-speaking countries, mainly Brazil and Portugal.
This worm is detected and blocked by Kaspersky Lab products as IM-Worm.Win32.FBook.a.





















IM worm targeting Brazilian Facebook users