
Looking up definitions for ‘iframe’ does indeed give results about “… a constraint of the H.264 codec specified by Apple to ensure ease of consumer video editing.”. Such iframes do contain all necessary rendering information and serve as reference to construct other frames. But here we discuss the other kind of iframes – HTML tags. Iframes can have several attributes and we often encounter them when analysing malicious sites. They are often used in a hidden way to construct drive-by downloads of malware. To hide even more, simple encryption (also called ‘obfuscation’) is often used, web browsers decrypt that on the fly. Knowing that, we can search for interesting websites. For example doing a web search for “#64#6f#63#75#6d#65#6e#74#2e#77#72#69#74#65” (which decodes to ‘document.write’), we instantly get 10,000+ results.
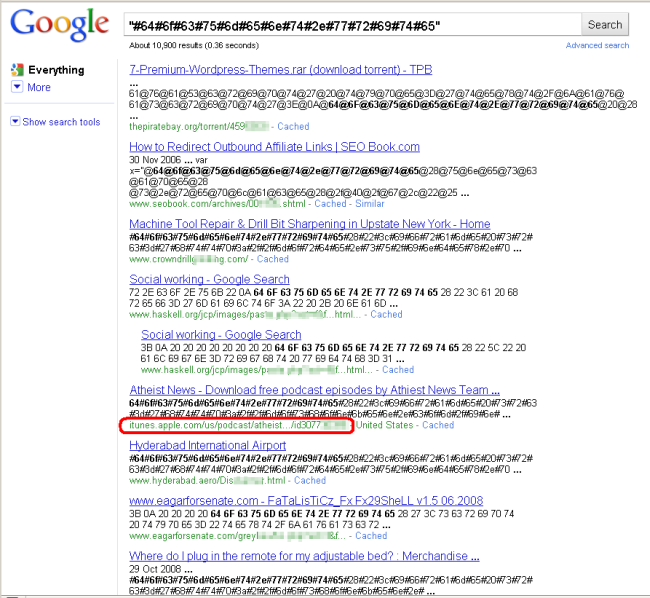
The first entry in our search results is a link to a torrent site where users discuss a malicious package.
Ironically in between these search results we also noticed what seems to be an ‘infected podcast’ hosted at itunes.apple.com – which brings us back to the initial talk about iframes. The injected code contains an iframe redirecting to moshonken(dot)com, a host known for having spread exploits in the past. Currently that host appears to be not operational but malicious code trying to access it is still injected in many legitimate sites, as our search results showed.
We detect this code as ‘HEUR:Trojan.Script.Iframer’ and have reported the problem via Apple’s feedback form.






















iFrames = Apple too?