
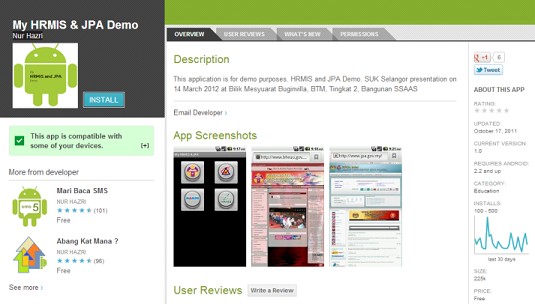
In mid-February 2013 a Kaspersky user from Malaysia asked us to check a Google Play application called My HRMIS & JPA Demo developed by Nur Nazri.
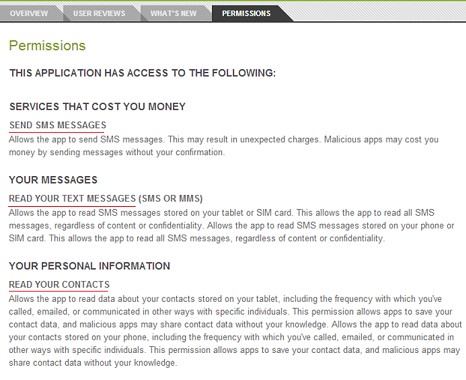
The user was suspicious about the large number of permissions required by the app, though its only stated function was to open four websites.
After launching the app shows these four buttons:
Clicking on one of these images opened the corresponding site in the standard Android browser:
Button 1 opens http://www.bheuu.gov.my/puspanita/;
Button 2 – http://www.jpa.gov.my/;
Button 3 – http://www.mampu.gov.my/web/guest/;
Button 4 – http://www.eghrmis.gov.my/.
But this is just what the user sees – there is more going on behind the scenes that he doesn’t know about. Clicking the app’s 2nd button opens the site, but also steals the last 10 contacts (names and numbers), and after clicking the 4th button the app first steals the three most recent incoming messages before opening the web page.
In both cases the data is stolen with the help of a text message sent to 0187109971.
The spyware targets Malaysian users, which is confirmed by our KSN service data – we only saw installations in Malaysia.
We detect the application My HRMIS & JPA Demo as Trojan-Spy.AndroidOS.Nuhaz.a and have informed Google’s security service of the threat in their app store. The malware has already deleted from the store.
PS The same author has two other programs in Google Play:
These apps are “legal spies” detected as not-a-virus:HEUR:Monitor.AndroidOS.Crakm.a and not-a-virus:HEUR:Monitor.AndroidOS.Lambs.a.
























Hello from Malaysia