
Phishing is not exactly a ground-breaking technique. Quite the opposite, it seems like it has been around forever. This is an indicator of its effectiveness: we might think that it is unlikely that people would give away their banking credentials just because they are asked for them, but still there is a percentage who continue to become victims of one of the simplest fraud methods.
However both user awareness and anti-phishing tools are making harder for fraudsters to succeed in their attempts to get our money. We see this changing in the decrease in the percentage of spam. That is not the only reason: users are switching to new platforms such as social networks for direct communication.
Today I want to show you an example of the creativeness in avoiding spam and phishing filters.
I already talked here about how cybercriminals abuse existing online services for both minimizing their operational costs and avoiding detection. In todays example they abuse Google Docs for phishing.
The procedure is as usual: an email with a malicious link. However no anti-phishing filter would ever consider GoogleDocs as malicious:
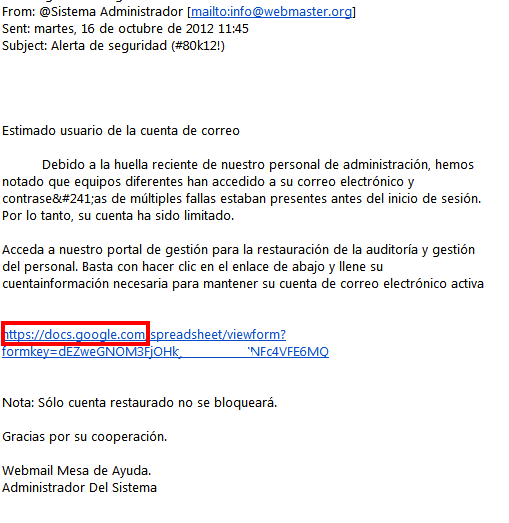
The email is poorly written in Spanish. If you follow the link you will reach a Google Doc (hosted by Google):
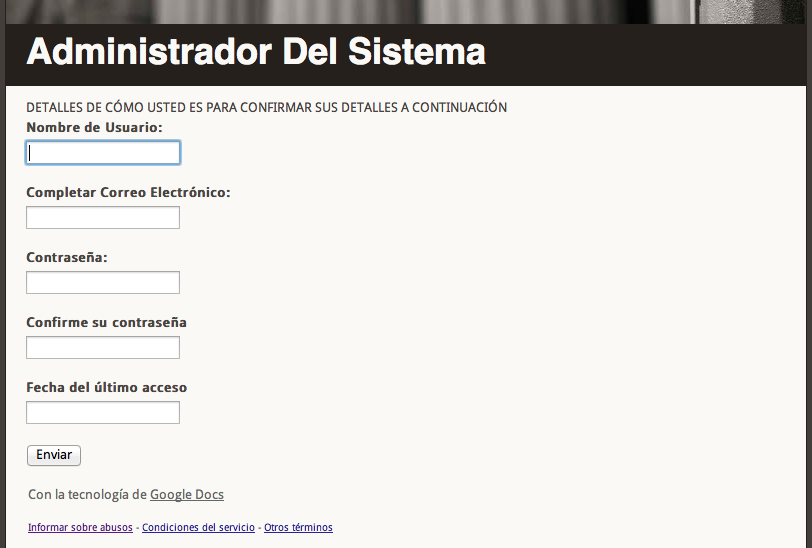
where victims are asked for their username, email, password (twice) and date of last access. The attackers target is not very clear, it looks like they are trying to steal email credentials.
As previously said, this Doc is created and hosted within Google Docs. In the event that someone inputs data, it will be sent to the Docs owner.
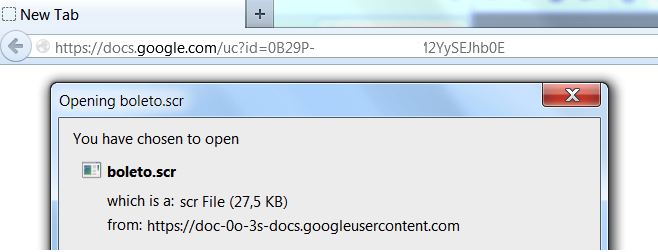
But this is just the tip of the iceberg. Google Docs allows hosting other contents such as executable files in different formats, resulting in a very convenient and free hosting service for malicious content. As a bonus the connection is HTTPS by default, making it even more convenient for cybercriminals the use of this service.
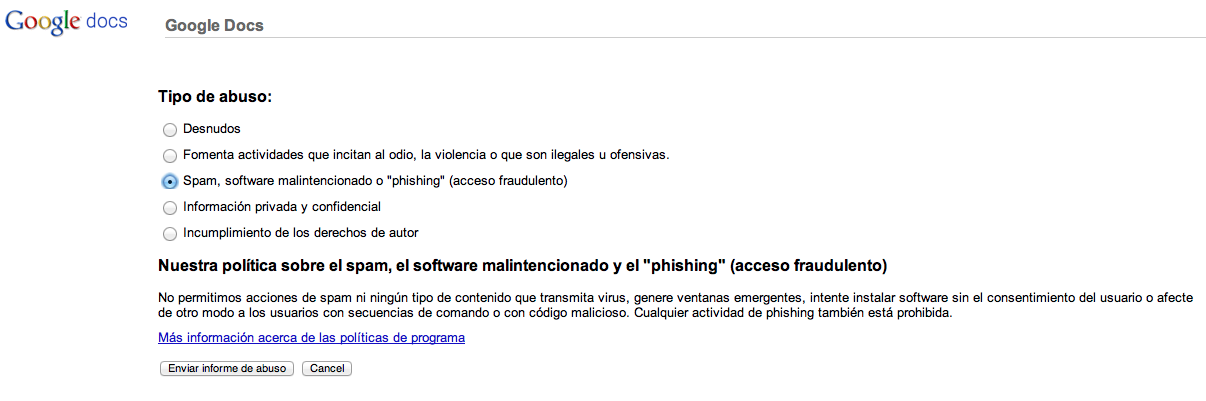
You can see how Google offers the option to report this as malicious content, which I have already done.
I thought the use of this method was not really mainstream. It shows how security could be bypassed by abusing legitimate services. The key for cybercriminals is to do it in such a way that they can fly below the radar and avoid being detected, so this method looks more dangerous for targeted attacks.
However after checking the data collected by my colleagues Im not that sure. It is much more common than I previously thought, as it is very effective in both avoiding defenses and looking legitimate content in the eyes of the victim.
PD: Thank you to my colleagues Fabio and Michael for their help in this post!






















Fraud abusing Google Docs