
The Ekoparty Security Conference 2013 was held in the beautiful city of Buenos Aires, Argentina, from 25 to 27 September, This event,the most important security conference in Latin America, is now in its ninth year and was attended by 1,500 people. The slogan of this year’s conference was “Somebody is watching”.

As every year the event took place at the Konex, a cultural complex created from a factory and oil tank in use from 1920 to 1992, which gives it a unique atmosphere for hosting the event.

Like Defcon and other security events, the presentations cover a wide variety of topics and discussions, Ekoparty is a forum where many security professionals present diverse research and development in Information Security.
Prior to the event there were some training courses for companies and security professionals, with content related to Defensive Security, Digital Forensics, Malware Analysis or Pentesting – among other topics. At this time I had the opportunity to present the training “Implementing Threat Intelligence in Organizations”, related to the implementation of strategies for monitoring, detection and defense. This was attended by security personnel of banks, e-commerce companies and government.
The first day began with a discussion panel about “The state of cyber-attacks and cyber-defense in Latin America”, with the participation of regional experts on this topic. In the evening there were workshops, with all auditoriums filled to maximum capacity. I presented the workshop “OSINT scripting intelligence”.

As with any security event, Ekoparty has its CTF (Capture The Flag) competition, but on this occasion it had a particular component that made it different to others. In this case, the competition was based on scenarios of attack and defense in which the participants not only earned points by capturing a flag, they could also lose points by not being able to defend themselves, or when several teams attacked them. In addition, a team could transfer points to another team, which turned into a very interesting strategy game.

On the second day the conference presentations began. All of them were very interesting and with great content and research, so I will touch on some of them.
Corey Kallenberg presented “Defeating signed BIOS enforcement”. He talked about how a BIOS system can be compromised beyond the protection of manufacturers. Later Harri Hursti presented “Vote early and vote often”, His talk was very interesting because at this time many countries have already implemented electronic voting systems and others are currently testing prototypes for deploying them.
He showed a series of vulnerabilities found in these systems, which may allow unauthorized access to display results, the manipulation of information or even the violation of the privacy of citizens. He even demonstrated the possibility that it was possible to generate Denial of Service attacks against these systems, preventing people from voting.
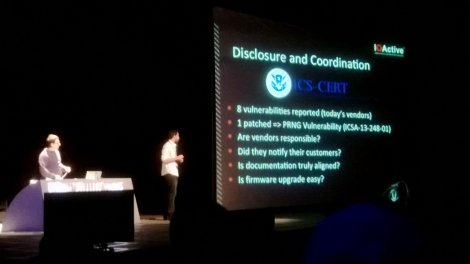
Also on the second day, Francisco Falcón and Nahuel Riva from Core Security gave the presentation“Do you know who’s watching you?: An in-depth examination of IP cameras attack surface”. They showed some of the vulnerabilities of web cameras from major manufacturers and showed us the perspective of how many times people choose poorly implemented solutions that can become a great risk to security and privacy.
Corey Kallenberg gave a presentation,“BIOS Chronomancy”, about how a BIOS system can be committed through persistent malware on certain computers, compromising systems beyond the operating system and applications.
Finally, to close the event, Carlos Penagos and Lucas Apa of IOActive presented an interesting talk,“Compromising Industrial Facilities From 40 Miles Away”, about vulnerabilities in wireless communications with sensors of industrial SCADA systems reading and injecting data into these devices using radio frequency transceivers (RF) within a range of 65 kilometers. In addition, they presented a POC in a simulator about how an attacker could manipulate the temperature of these sensors, causing a disaster by increasing or decreasing the temperature.
As with all the great security events, we had good talks and we learned from the new research of our colleagues. But Ekopary has a Latino flavor that makes it different. This was a great event and you may be interested to attend future editions. You will really enjoy the city and of course an “Asado” with colleagues and friends 🙂




















Ekoparty Security Conference 2013