
It’s been clear for a long time that virus writers will take whatever opportunity they can to spread their malicious code. One popular approach is exploiting public holidays and other well-known days on the calendar – the St. Valentine’s Day spam this year is a case in point.
The approach is particularly effective if the holiday is an international one – the result is an increased pool of potential victims.
Last night, on the eve of April Fool’s Day, we started seeing a wave of new modifications of the notorious Zhelatin worm. At the time our mail pots started picking up on these messages, no antivirus company was detecting the latest version of the worm.
This latest attack took the usual approach:
1: Prepare the bot machines
2: Mass mail spam containing a link to a site
3: Malicious code is automatically downloaded to the victim machine when the site is viewedOne of the latest examples of such sites is shown below:
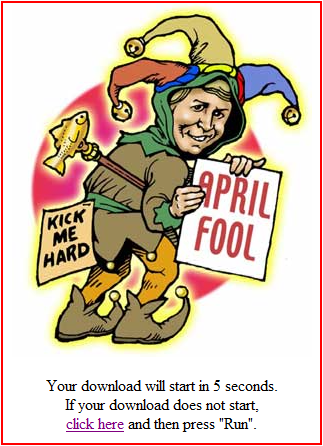
If for some reason the malicious code doesn’t automatically download when the user views the page, it will be manually downloaded if the user clicks either the image or the hyperlink. The name of the malicious file varies: some of the recent examples are funny.exe, foolsday.exe and kickme.exe. The size of the file also varies depending on the precise variant of the malicious program, but it’s usually around 137KB. We detect it as Email-Worm.Win32.Zhelatin
Not only do the bad guys have complete control over the bot machines, they also – naturally – keep an eye on what the antivirus world is up to. Once the most recent variant of the malicious program starts being detected, a new variant will be placed on the site. And while they’re watching us, of course we’re watching them, tracking the activity on such sites.
I’ll close with our usual warning: make sure you keep your antivirus databases up to date, and even though April 1st is a day for fun and games, you shouldn’t forget about security!




















Don’t be an April Fool!