
Two approaches to protecting virtualized data centers
Virtualized environments are exceptionally flexible, manageable, fault-tolerant and cost-effective. However, a number of difficulties have to be overcome to protect them from external threats. If this is not done successfully, problems will inevitably arise. This is true of individual virtual machines, as well as the data center as a whole.
Unfortunately, malware infections are a common occurrence in virtualized systems, particularly in VDI environments: customers’ employees do whatever they like on their virtual workstations without worrying about cyber-hygiene, believing that both their own IT department and the service provider will effectively block any malware.
It should be noted that, in most cases, the provider is not allowed access to customer machines and has to demand that customers use their own protection. Many customers, though not all, take a responsible approach and install endpoint protection solutions of their choice on their machines.
Sometimes, however, in spite of the provider’s recurring requests, customers resign themselves to the risk and do absolutely nothing about protection. There is no doubt that the provider will ultimately have to deal with all the problems arising from this approach. As a result, this turns into a major undertaking for the provider, who will have to change its protection strategy completely. (More information about security-related business problems faced by data centers can be found here.)
In virtualized data centers, information is stored and processed on virtual machines and in data storage systems. These are completely different technologies that require different approaches to protection, each having many subtle aspects.
The nuances of protecting virtualized environments
As mentioned above, if the service provider does not provide protection for customers’ virtual machines, customers will do it on their own, each in their own individual way. On the one hand, this is not a bad thing; each customer can choose a security solution that suits their needs. However, in practice, this approach is not only inefficient; the resulting chaotic ‘zoo’ of solutions on customer machines creates numerous problems of its own:
- Excessive use of hardware resources. The security system on each machine includes a complete set of components: an antivirus engine, a signature database, a firewall, etc. Each takes up its share of CPU time, RAM and disk space.
- ‘Storms’. If scanning for malware is performed or antivirus databases are updated on several virtual machines at the same time, this leads to a surge in resource consumption, which can result in degradation of the entire platform’s performance or even in denial of service. Security software can of course be manually configured to avoid storms, but the time required to do this for hundreds of virtual machines will be very significant.
- Panic attacks. A security system is often configured to step up protection when malware is detected on a machine. A ‘paranoid’ set of security rules is activated and out-of-schedule scans are launched. This can increase the load on the host machine’s hardware and negatively affect the performance of neighboring virtual machines.
- ‘Instant-on’ security gap. Virtual machines often remain inactive until they are started up when the need arises. While a machine is inactive, none of the security system components on it are updated and the machine remains vulnerable during the period from startup until an anti-malware solution update is completed.
- Incompatibility. Virtual machines are similar to physical computers in many ways, but they are also different in some significant aspects of their operation. For example, they use dynamic hard disks and can migrate from one server to another without shutting down. Standard security systems for physical machines are not designed with virtualized systems in mind. This can lead to delays, faulty operation or even complete inability to operate.
All these issues will ultimately have to be addressed by the service provider – and on a regular basis. There is only one way to avoid this – prevent this ‘zoo’ from being created in the first place by putting customers in a situation where they have to choose between several proven dedicated security solutions for virtualized environments.
With or without an agent?
The key advantage of virtualization security systems like Kaspersky Security for Virtualization lies in the fact that the engine and the anti-malware databases are hosted on a separate virtual machine (Security Virtual Appliance, SVA) which provides protection for all machines running on the hypervisor.
This solution has obvious advantages: hundreds of machines can be protected by just one anti-malware engine running on the SVA, which operates all the time and receives timely updates. This means all machines receive a high level of protection, while the VM scanning schedule is designed to preclude any excess load on the environment.
Virtualization security software can be implemented in two substantially different ways: agent-based (light agent) or agentless. Customers have the freedom to choose the one that best suits their needs, or even combine the two.
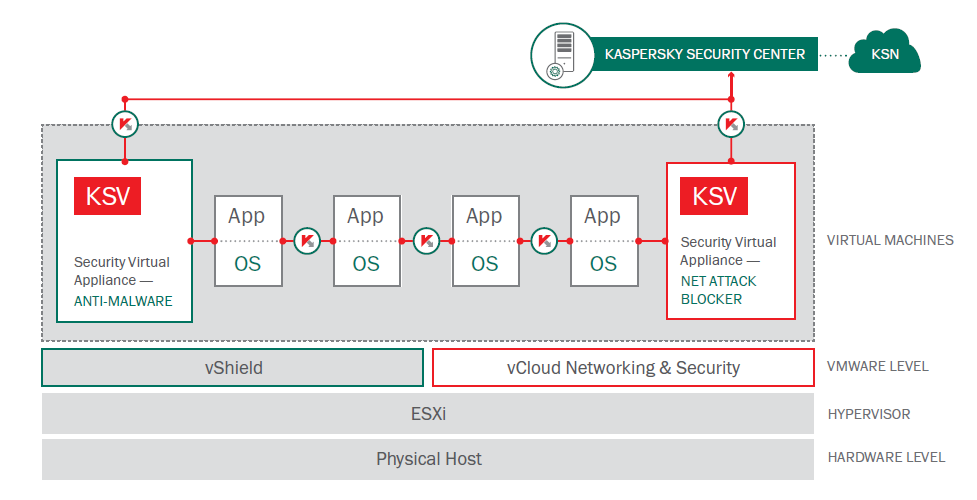
The agentless security solution has all of its components running on the SVA, and has a number of serious limitations. It is only designed to operate in environments based on VMware products, and is not capable of working with processes running in virtual machine memories, so it only scans the file system and incoming network traffic. In other words, it can only scan files and block network attacks. In some cases, this is sufficient. An agentless solution also provides almost instant protection of virtual machines immediately after they are launched. No software needs to be installed on the customer’s machines.
The agentless approach to securing virtual environments, based on the solution Kaspersky Security for Virtualization | Agentless
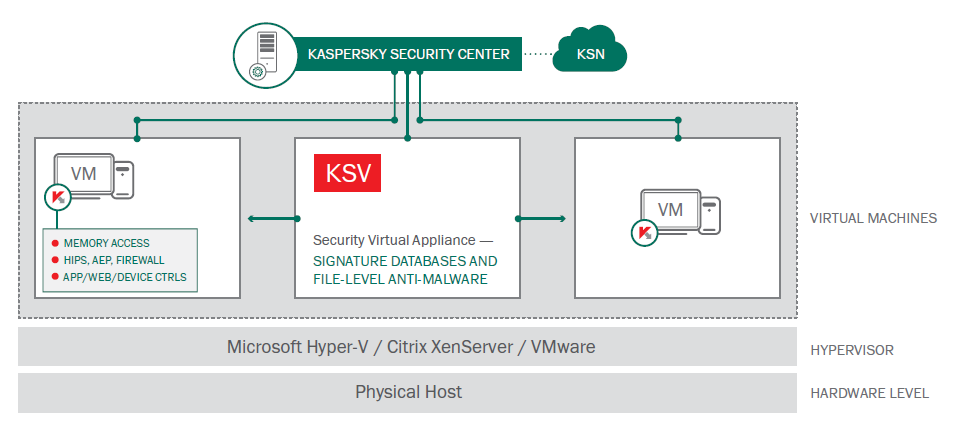
The light agent-based security system provides the entire range of security technologies (working with memory processes, application control, web browser protection, etc.) without using up lots of resources, as the scan engine and the databases are hosted on the SVA. Such an approach provides the functionality similar to Endpoint Protection-class solutions, while also being optimized and tested for virtual environments. However, a lightweight agent needs to be installed on each virtual machine so that the security solution has full access to the system. This can be seen as inconvenience, but many virtualization scenarios allow the use VM templates; in this case, the agent can be pre-installed into the template, so every VM spawned from it would have the agent as well, receiving instant protection right after being started.
The light agent-based approach to securing virtual environments, based on the solution Kaspersky Security for Virtualization | Light Agent
The choice between these two types of solutions depends on the accompanying circumstances.
Often the provider cannot guarantee the presence of a security solution at the customer’s facility, which potentially creates a gap in data center security. The customer may also have reasons for not allowing any third-party software to be installed on their machines. In this case, the agentless security solution is the optimal choice.
In other cases, the provider and the customer agree from the outset that a security solution will be installed on the virtual machines from a shortlist of tested and approved solutions. In this case, it is best to use specialized light agent-based security systems for virtual environments. This will provide the maximum level of security with minimum collateral problems.
A special case is that of a virtual desktop infrastructure (VDI) hosted in a data center. When virtual machines are used as workstations, each of them is exposed to a multitude of threats during everyday operations. An employee may pick up a malware program when visiting a dangerous website or receive an email with a malicious attachment, while it is not uncommon for malware to spread from a removable media device that has passed between other users.
When such a broad range of potential infection vectors is present, an agentless solution will be insufficient: with its limited functionality, the risk of infection is much higher. If an infection is detected, it will most probably happen too late to prevent any damage. On the other hand, a light agent-based security system is capable of protecting against a much broader range of threats by checking programs that are launched, preemptively blocking a user’s access to dangerous websites, and controlling the processes running in the system.
A third, more resource-intensive, protection option for virtual machines also exists – a ‘regular’, full-agent endpoint protection-class security product. This is a viable choice if there is no access to the hypervisor (e.g. in public clouds such as Amazon or Azure), or if a more obscure hypervisor is used at the data center that is incompatible with specialized security solutions. And finally, these ‘regular’ security systems are developed for a broader range of operating systems. For instance, they can be used to protect virtual machines running under Mac OS.
It should be noted that a security system that is not designed to work in a virtual environment may not be fully compatible with specific virtual machines and may not work properly or may not work at all. Solving these types of issues can take considerable time.
Taking care of data storages
An infected network data storage puts the entire data center at risk, and if anything requires anti-malware protection, it is data storage systems. If this need is not fulfilled, an epidemic may break out, especially if not all the machines located at the data center are connected to a security solution for virtual environments.
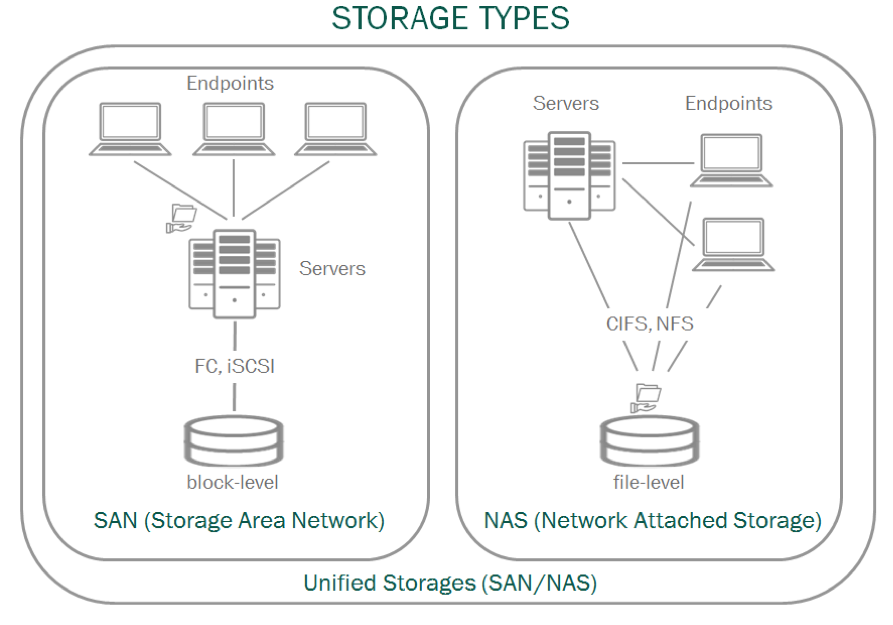
Storage Area Networks (SAN) are very easy to protect – all it takes is a security system on the server. This is no different from protecting any other server; in this case, a server solution is implemented, such as Kaspersky Security for File Servers. Things are different with Network Attached Storage (NAS), which all machines in the network are granted instant access to. In this case, a specialized NAS security solution is required.
Network data storage types
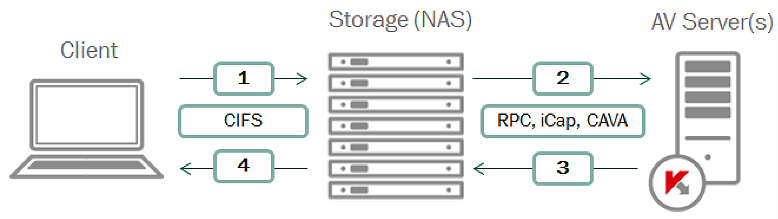
Data stored on NAS needs to be protected before it is available to customer machines, meaning support on the NAS side is required. Luckily, most NAS support a number of special protocols and are able to work with external security solutions.
Diagram showing how a NAS protection solution works
When a customer requests a file from NAS (1), the storage sends it to the security system’s server (2). The server scans the file and reports the result to the storage (3). Depending on the security solution’s verdict, NAS provides the file to the customer or denies access (4). For greater reliability, more than one security server can be present in a network. During normal operation, the data storage itself will balance the load between them.
Conclusion
When it comes to securing virtualized data centers, there is no silver bullet solution, nor can there be one, that would ideally solve all problems. What is possible is to choose the optimum security system based on all the relevant factors.
An agentless solution is best for protecting database servers, intranet web servers and machines that are not allowed to host any software besides a fixed set of applications.
If the customer has a choice of several specialized security solutions pre-approved by the provider, a light agent solution is the best option. This will meet the needs of protecting web servers, virtual workstations, and sensitive data processing servers.
Flexibility is particularly relevant when protecting virtual environments, so Kaspersky Lab provides both solutions – the agentless solution and the light agent solution – under one license. This gives the customer a choice between these two variants, and the capability to combine them when necessary, e.g. in environments with different hypervisors, or to address a variety of tasks more efficiently. More detailed information is available here.
The most important thing is to ensure that protection issues are addressed before any annoying and costly problems arise.

















Disbanding the ‘Zoo’