
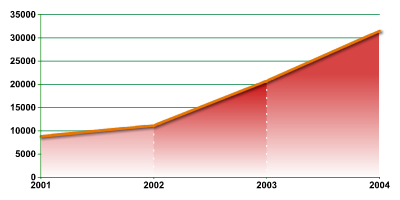
In spite of the steps taken by IT industry, the evolution of the Internet is
accompanied by the evolution of malicious code. Proof of this is our statistics on the number of new entries to the signature base for Kaspersky Anti-Virus.
|
Number of signatures added to Kaspersky Anti-Virus database every year (2001 – 2004) |
Our graph shows that the number of malicious programs continues to increase. And it seems certain that this trend will continue – and we will continue to detect increasing numbers of viruses, worms, Trojans and other malicious programs.
We will be publishing some more detailed statistics on our antivirus databases in the near future. Watch this site…





















Danger of infection increasing year by year