
It’s holiday time, and of course the bad guys know that shopping is a popular activity during this period, particularly in Europe and the US. And it’s in these regions that most people pay for their purchases either using credit cards, or e-payment systems like PayPal, WebMoney etc.
In order to target this data, cybercriminals create “universal” malicious programs, which will intercept all financial data, whether it related to credit cards, bank accounts, or e-payment systems.
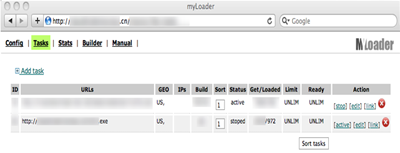
A recent case shows this clearly: a botnet made up of several thousand machines was used to install Trojan.Win32.Vilsel.qhw on 972 victim machines, all of which are located in the US.
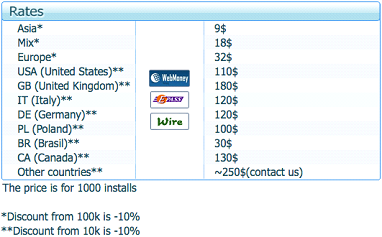
It seems likely that this botnet was rented specially in order to install this malware – a common practice in the cybercriminal world. There are plenty of places on the Internet which offer this “service”, as the screenshot below shows. In order to deliver the Trojan to 972 machines in the US, the bad guys would have had to pay around $100.
So where’s the profit in this? Well, the malware in question will intercept Internet transactions made using Internet Explorer and the new(ish) Chrome browser. That covers a huge percentage of Internet users, and because the malware targets a whole range of payment options, it won’t make any difference if payment is made by credit card or PayPal – confidential data will still get logged and then sent onwards to the bad guys.
Additionally, once it’s been run for the first time on the victim machine, this malware deletes its original file (to hide traces of infection); prevents access to Task Manager at system registry level, and also blocks Regedit, making it more difficult to manually check the system and identify and delete the malware.
According to VirusTotal, at the time of writing only 6/40 (15%) of antivirus vendors detected this threat, and a lot of the big names were among those missing.





















Cybercriminals go shopping