
This year cybercriminals haven’t been particularly active in exploiting the upcoming holiday season to snare victims with their scams. The first evidence of a growing trend of festive fraud only began to emerge about a week ago. Interestingly, this year’s attacks are somewhat different from previous years. This time round cybercriminals aren’t just going for hard cash – they are also looking for other assets that can be converted into money, such as air miles.
In Latin America, we have seen several festive-themed attacks that were in some way linked to air miles.

It’s also worth remembering that there were malicious email messages mass-mailed to English-language users a couple of weeks ago using fake American Airlines tickets as bait.
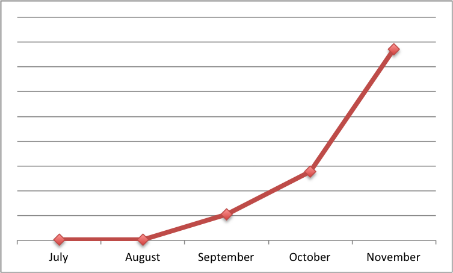
Obviously, these virtual products are popular with cybercriminals. We first detected attacks like this back in July 2011, and their number has been on the increase ever since.
In some cases, cybercriminals make money from their victims without causing any direct financial damage. For example, this year we have seen numerous Clicker Trojans disguised as Christmas-themed search services.
In general, the black cybermarket works just like your local High Street: there are discounted prices (keyloggers offered at a 50% discount), online stores with their Christmassy interfaces etc.
The recommendations are the same as ever: be careful and stay informed about possible scams. This way you’ll minimize your chances of falling victim to cybercrime this Christmas.






















Cybercriminals celebrate Christmas with festive fraud