
You may have read about the Cryptolocker malware, a new ransomware Trojan that encrypts your files and demands money to return them.
In the past, we have witnessed similar malware like the famous GPCode that used RSA keys for encryption. Back in 2008, we cracked the 660 bit RSA key used by GPCode and provided the victims with a method to decrypt and recover their data. Later, the GPCode authors upgraded the RSA key to 1024 bits, putting it perhaps only in the realm of NSA’s cracking power.
Cryptolocker uses a solid encryption scheme as well, which so far appears uncrackable. For each victim, it connects to its command-and-control (C2) to download an RSA public key that is used to encrypt the data. For each new victim, another unique key is created and only the Cryptolocker authors have access to the decryption keys.

The attackers give you roughly three days to pay them, otherwise your data is gone forever. A multitude of payment options are available, including Bitcoin:

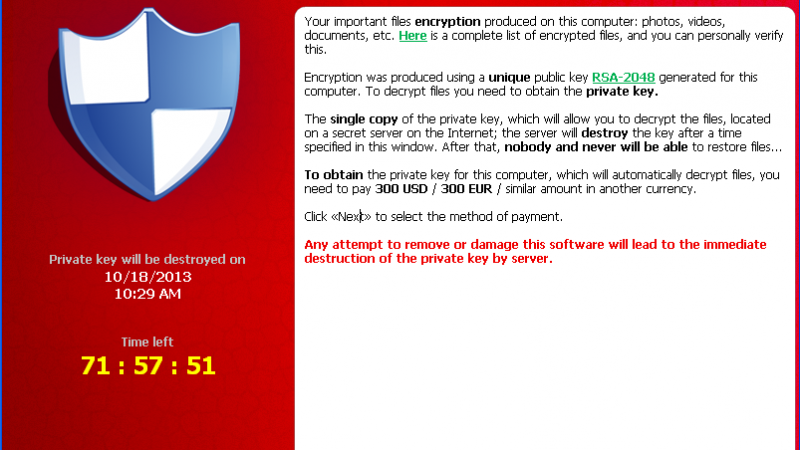
To make sure the victim gets the message, they set a pretty scary wallpaper on the infected machine:

To connect to the C2 servers, Cryptolocker uses a domain generation algorithm that produces 1000 candidate unique domain names every day.
Dimiter Andonov from ThreatTrack Security reverse- engineered the algorithm and Kaspersky Lab sinkholed three domains to measure the number of worldwide victims.
In total, we’ve had 2764 unique victim IP’s contacting the sinkholed domains.
The highest number was recorded on Wednesday October 16, with 1266 unique IP addresses.

Below you can find the distribution of victims per country – top 30. The most affected countries are the UK and US, followed by India, Canada and Australia:

It’s important to point out the statistics indicate the number of victims that haven’t had their files encrypted yet. If they act quickly after the infection and clean their system with an anti-malware tool, then the data might not be encrypted at all.
Defense strategies
Cryptolocker uses a solid method to encrypt files and to make sure their unencrypted versions can’t be recovered by tools such as Photorec. The best strategy is to make sure you are running an updated anti-malware product, capable of stopping the infection. The Kaspersky host intrusion prevention system is capable of blocking even unknown versions of this Trojan from infecting the systems.
For a free system check, you can use the Kaspersky Rescue Disk:
1. Download the ISO image of Kaspersky Rescue Disk.
2. Download the Kaspersky Rescue Disk Maker (rescue2usb.exe).
3. View documentation on Knowledgebase.
The most widespread variants of the Cryptolocker malware are detected by Kaspersky products with the following verdicts:
Trojan-Ransom.Win32.Blocker.cfkz, Trojan-Ransom.Win32.Blocker.cmkv, Trojan-Ransom.Win32.Blocker.cggx, Trojan-Ransom.Win32.Blocker.cfow, Trojan-Ransom.Win32.Blocker.cjzj, Trojan-Ransom.Win32.Blocker.cgmz, Trojan-Ransom.Win32.Blocker.cguo, Trojan-Ransom.Win32.Blocker.cfwh, Trojan-Ransom.Win32.Blocker.cllo, Trojan-Ransom.Win32.Blocker.coew.
If your data has already been encrypted, the worst thing to do is to pay the bad guys. This will encourage them to expand and strengthen the attack techniques.
As always, prevention is the best cure!
Cryptolocker Wants Your Money!





















Jaon Anderson
We have Kaspersky Total Protection 2017. Does this product protect against, find, and remove the ransomware mentioned in this post? I see this post is from 2013. Is there an updated post as well?