
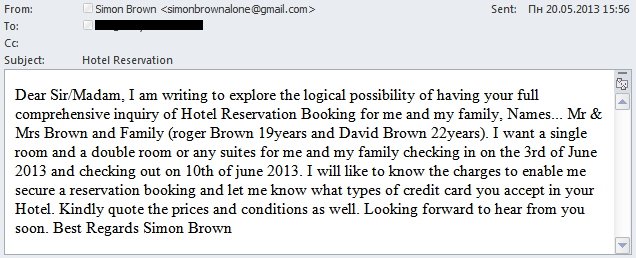
Lately, our traps have been catching emails like these:
In them someone with a very English name is asking to book a hotel or air tickets for their family. A naïve recipient would think “Ah, wrong address”.
A more experienced user would no doubt smell a rat. First of all, the email does not contain a personal appeal. Secondly, there is no hotel name or even the name of the country where the supposed visitor intends to stay. Instead, the message says “your country” or “your area”, which is typically ambiguous language used by spammers spreading mass mailings. Moreover, the language in these emails seems a bit unnatural which is unusual given that native speakers are supposedly writing them. The text contains grammatical and punctuation errors.
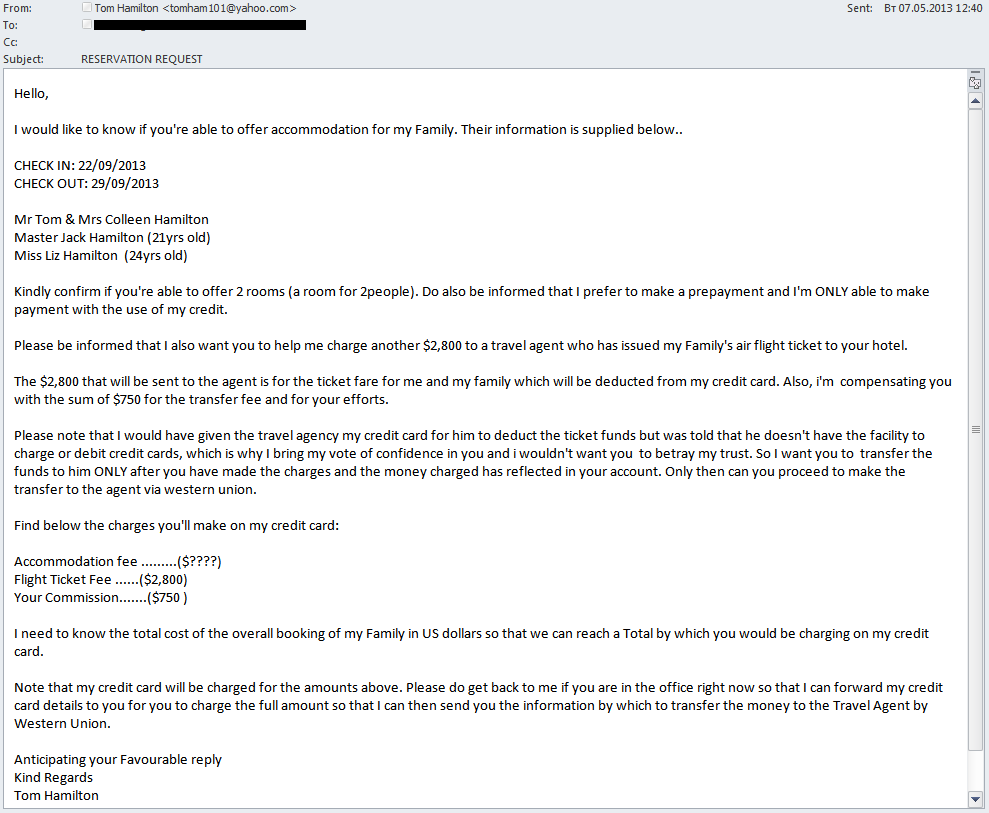
So, the email is suspicious, but what’s the catch?
In fact, this email is part of a fraudulent scheme used by cybercriminals to launder money from stolen credit cards. If the recipient of the email turns out to be a hotel representative and responds to the message, the fraudsters will send him/her the next email containing the credit card information and a request to withdraw a sum of money that considerably exceeds the costs to be paid for the reservation. The balance is to be transferred to a specified address via Western Union. The fraudster claims this is for the travel agent organizing the tour. The authors of the emails come up with various reasons why the agent can take payment from the credit card and why the potential tourist cannot conduct the transfer himself. Shortly afterwards, the fraudsters cancel the reservation, getting back the other part of the withdrawn sum (now laundered and “clean”).
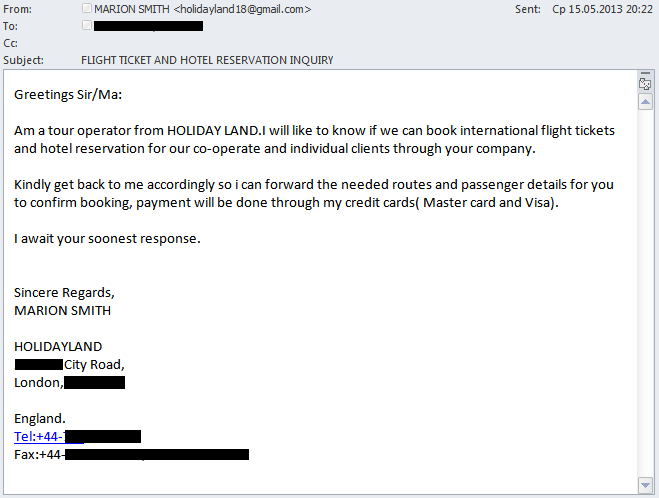
Sometimes the name of the travel agent is mentioned in the first email:
Typically, such messages arrive at corporate addresses. Email addresses containing specific words such as ‘info’ are especially prone to these emails. The addresses of the senders are registered on free email services (mainly Yahoo and Gmail). If the addressee responds to at least one email, then they will start appearing in his/her email box with surprising regularity. This type of fraud is a lesser-known variant of the Nigerian scheme. It has been around for many years, although previously cybercriminals preferred to send hotel managers fake checks and then cancel reservations getting back real money. Now, with the widespread development of online banking, stolen credit cards are mostly used.
We strongly recommend users to delete such emails. Hotel employees should be especially careful because getting involved in a scam like this could result in criminal charges related to money laundering.


















Caution! Fraud!