
When logging into Facebook this morning I saw that many of my friends posted a link to a video on their wall, and also everyone liked the link. The video was of a girl with a nice butt and it had the title “Laura Frisian: the most beautiful ass in the world!”, it was pretty obvious that it was a scam because it looked like all the other Facebook scams we have seen, but because soo many of my friends were posting this video I still decided to take a look at it.
I quickly ended up in a JavaScript hell, with obfuscated code and multiple domains. It seems that the server used in this scam is hosting about 300 pages similar to the one im writing about. All of the pages look the same, but have many different videos, a few examples are:
- If you like Nutella, never look this video!!!
- Drill a tooth abscess! Disgusting :s
- Compilation of Embarrassing and Busted! Photos, Awesome 😀
- Transgender 10-Year-Old, Boy Happier As A Girl !
- A Really Giant Baby ! Amazing it looks so real 😀
- Air Race Plane Crashed in the crowd during a show !
- The worst thing that can happen to a girl!
- A fisherman catches a couple when they make … 😀
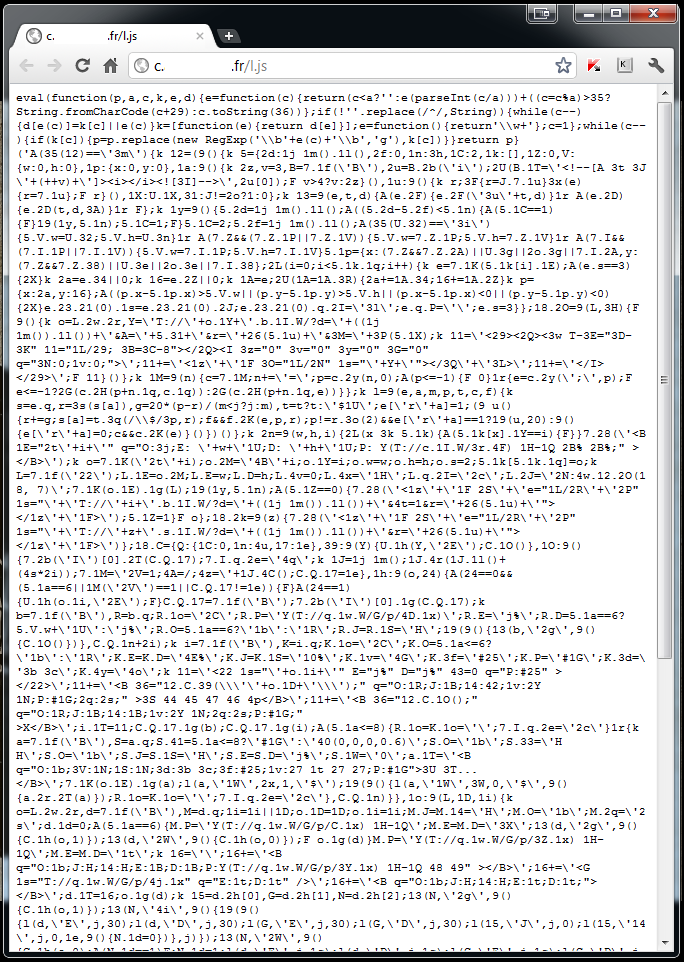
There are also many different JavaScripts being loaded, one of the ones we have identified is the following one, and exactly what this one does is not clear yet:
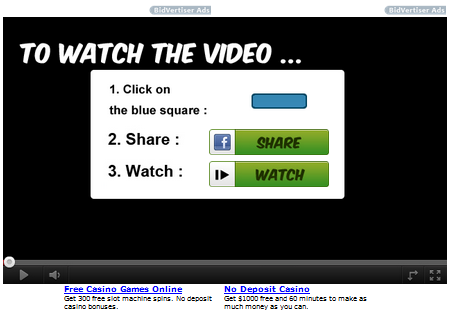
But the synopsis of the scam is pretty simple. If you click on the link to the video you will end up on a splash page, on this page you will be exposed to a clickjacking/likejacking attempt. This means that if you try to watch the video, or any other video on the page it will automatically post things on your Facebook wall. This require that you are logged in to Facebook or have been logged in and your cookie is still active. There are two different splash pages, one if you are loggedin to Facebook, and one of you are not. Please see screenshots below:
If you are not logged in to Facebook

If you are logged in to Facebook
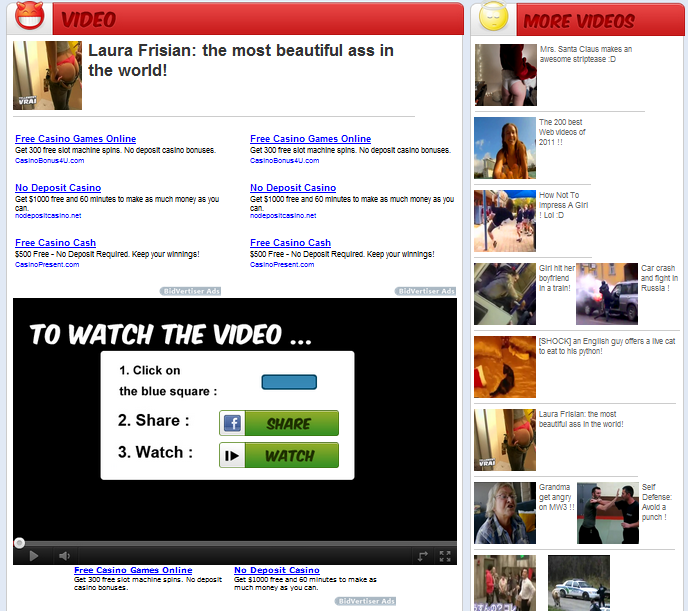
The full landing page looks like this:
The JavaScript code is obfuscated and packed, this makes the entire debugging more difficult, but during the research I have identified several domains connected to this scam. It also seems that they use redirectors to prevent URL/Domain denylisting, and there are also several different scams on each server.
It seems that the purpose of this scam is to expose you to ads, and also automatically get you to like certain ads. This will generate both traffic and money for the guys behind this.
Please, if you see this on Facebook, please report it as spam, this will allow the Facebook Security Team to deal with this much faster.




















BuzzMania – ClickJacking / LikeJacking spam on Facebook!