
How much do you earn per day? If we look at how
much a cybercriminal from Brazil earns every day, we’ll understand
why Brazil is one of the main sources of malware in the world.
Brazilian cybercriminals really like to use short URLs to track
infections and have their own stats. Here is the profile of one
criminal using Bitly as a URL shortening service.
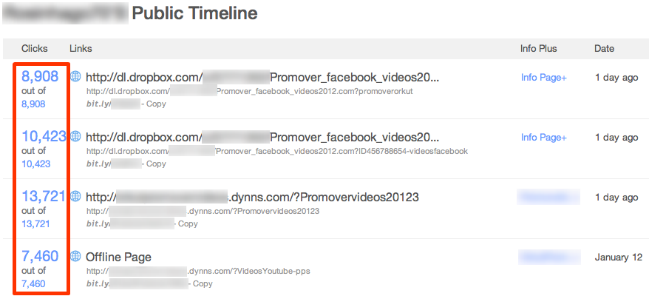
As you can see, in just one day, he was able to gain more than
33,000 clicks or potential infections! Let’s presume that just 10%
of all the victim machines end up getting infected. That means
approximately 3300 people are affected. In Brazil malware is usually
spread in order to steal only credit card and online banking account
information, and this was the case with this particular campaign.
Account information for other Internet resources like Facebook, IM,
email etc. was not stolen.
So, how much did the criminal make on that particular day? Let’s
see: a
unit price on the black market for stolen Brazilian credit
cards is about $8 USD. Now let’s suppose that the average
savings in a bank account amount to about $500 USD. Cybercriminals
from Brazil don’t sell access to the stolen bank accounts; they use
the accounts themselves, cleaning them out completely. After some
simple math (3305
* 8 * 500) we get a daily earnings figure of $13220000 USD! Of course it will
take some time to cash this money in, but the sum is enough
motivation to get the work done.
Of course, in real life the rate of infection would be higher than
just 10%. In most cases it can easily be between 50 and 60%.
The lack of legislation in many countries like Brazil makes it
possible to steal huge amounts of money with little risk of going to
jail.






















Brazilian cybercriminals’ daily earnings – more than you’ll ever earn in a year!