
A relatively new development in app advertising has a concerning feature. It leeches much of the same information that many Android Trojans also steal. Through an app promotion campaign, a new feature called “offerwalls” are used by Pay Per Install (PPI) services to promise further adoption and revenue for app developers. But what is the real danger? It is found in the way these services uniquely identify users and the information they collect.
What is Pay Per Install?
Pay Per install within the Android App world, is a service offered by specialized advertisers to app developers with the intention of further exposing their apps to a larger audience. Many services exist, such as Tapjoy and Everbadge, which, in the latter case, promises to increase app revenue by “50-400%”. These sites use a particular method of tracking users. App developers need to enable this tracking somehow. In most cases, an SDK (software development kit) must be installed. Tracking code is added to the developer’s application, and that code is supplied by the PPI site.

What is an “Offerwall”?
To further entice users to keep playing games, or to try new apps, the “offerwall” was invented where developers can offer points, virtual goods, or even currencies. In many cases, this is simply a place where users who complete certain amounts of a game, or complete various tasks, will be awarded a badge or some type of virtual reward as well as advertising other apps. This offerwall is displayed within the downloaded application. For each task accomplished, new badges are attained. This is only one use case, and a far more familiar version of this type of tactic can be found on sites like Facebook, in games like Farmville, or similar.
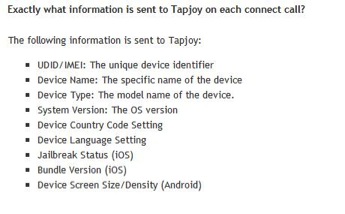
What information is shared?
For these types of campaigns to work, the users of the apps must be uniquely identified in some way. A unique ID is assigned to each user and these ID’s are sent back to the advertising service. In many cases these apps request a large amount of personal data such as Contact data, Calendar events, the ability to send email, and the ability to send SMS messages. How much of this data is collected by the advertisers as well as how it is used, is unclear, and the possiblilty that this data is collected by more than just the app developer is never explicitly stated.
What can this information be used for?
This type of data, along with the ability to uniquely identify specific phones presents an interesting problem for end users. It’s a great example of why users need to be so careful when examining requested permissions by particular applications before they install them. It is unclear why many of these apps would require the ability to send SMS messages. Many of these apps also use geographic location identification. When third parties are able to identify a user, their contacts and their precise location, user safety, privacy and anonymity are at risk.
What can I do about it?
Examine app permission requests very carefully. If apps contain “offerwalls” treat them as suspect as they may be siphoning off data you never intended to share. Read reviews from other users carefully, and if you already have these apps installed, monitor your personal information carefully as well. With the explosion in popularity of mobile apps, and the consequent advertising industry following it, it is becoming increasingly hard to define what constitutes spyware. Buyer beware.


















Are “Offerwalls” siphoning your personal information?