
While Google is obviously trying to create a safer environment in regard to the Android operating system, some of these changes are leaving me a bit confused. I recently discovered some interesting behavior in regard to the default email client in 4.0 Ice Cream Sandwich.
It seems that if you try to download or open a zip file attachment from within the email client, Google warns of the possibility of malware:
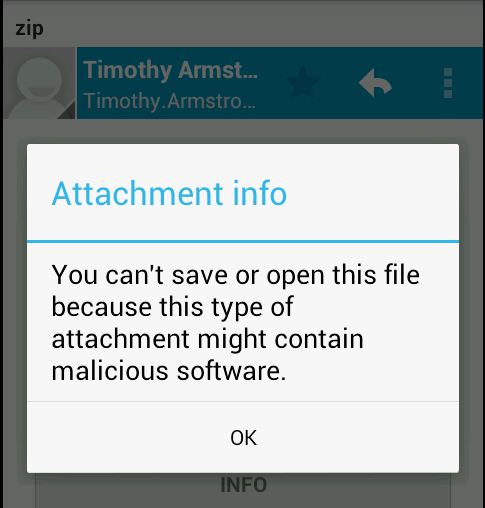
Well I suppose a zip file could contain malware, or any number of other things like pictures, text files, you name it.
So I decided to see what happens if I sent myself an APK file, the default installer file for Android apps, and then tried to open the attachment:
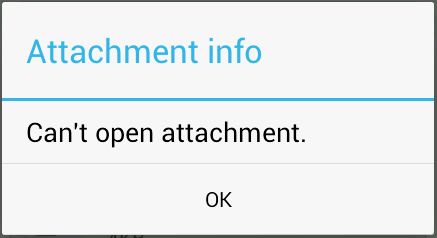
Now that’s interesting. I’m just not allowed to open it. I tried with multiple APK files and was delivered the same result.
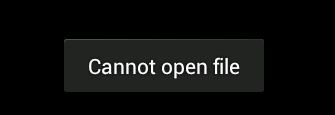
I then decided to test this behavior from the mobile browser. After logging into my test email account (which is the same I used in the previous tests) I happily downloaded the zip file from the web, but I still could not open it:
However, I was able to download the APK file, and after the download completed I was taken through the standard installation screens:
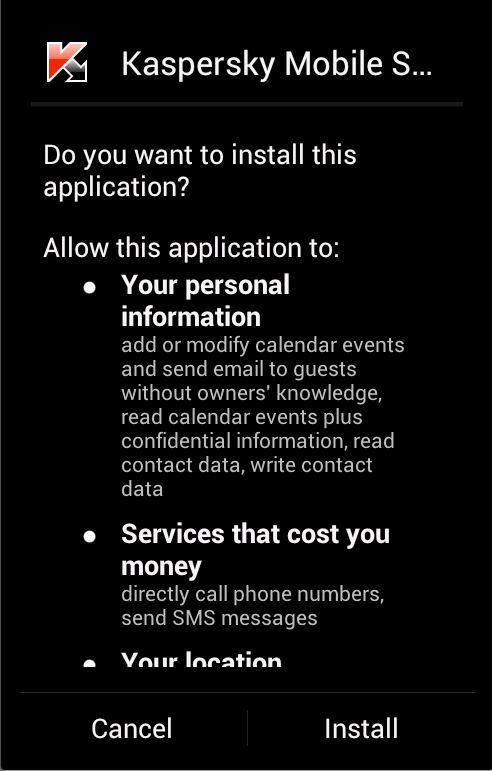
As you can see, while the concept is headed in the right direction, the execution is mediocre at best. Why prevent downloading and opening zip files? Why not provide the same restrictions on APK’s downloaded from the web? It appears to me that Google still has some implementation issues when it comes to protecting users.
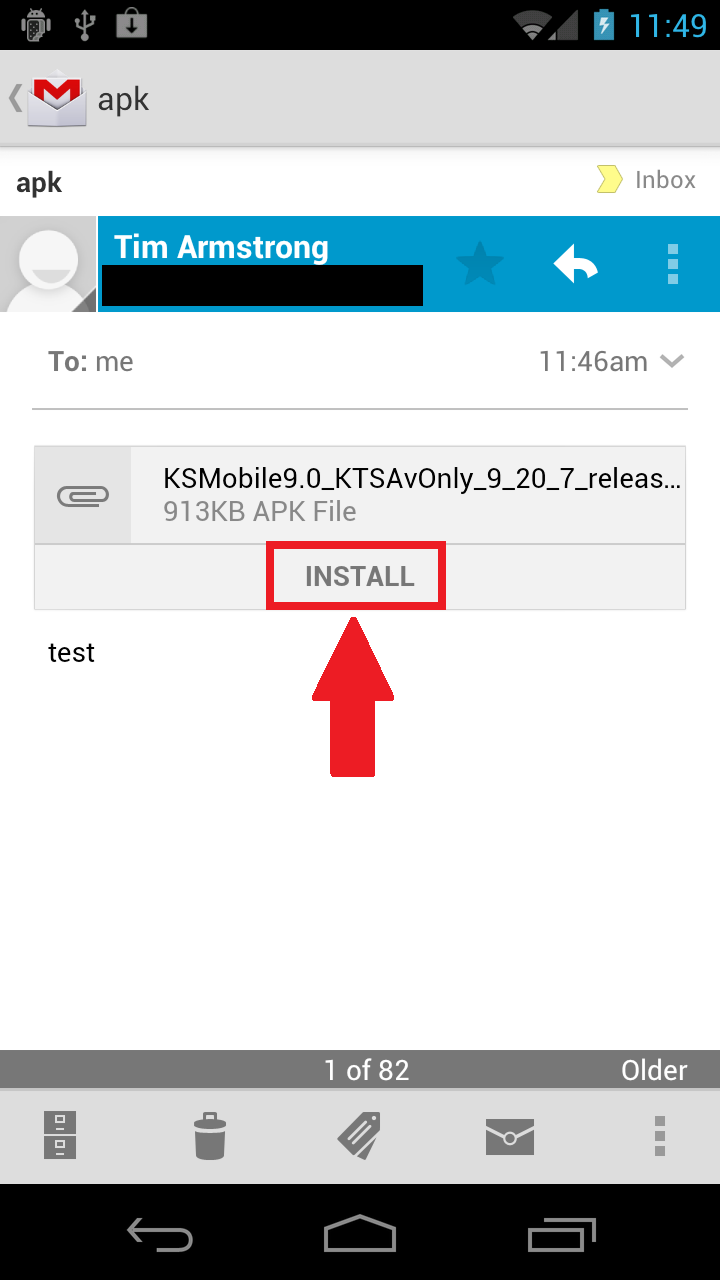
It should be noted that all of these tests were done with the Android emulator using the latest available version of Ice Cream Sandwich. When I sent the same APK to my physical device running Ice Cream Sandwich and opened it with the gmail app I was offered an Install link. This all seems very inconsistent to me.
Special thanks to my colleague Roel Schouwenberg for assistance with testing.



















Is Google confused about Android security?