
Airport kiosks have achieved a wide distribution nowadays. They offer the convenience of having access to all sorts of travel related information, IP-telephony as well as to the Internet while on the road. Which is a good thing!
However, when I travelled back from BlackHat and DefCon 19 and checked in at the Mc Carran airport in Las Vegas, one of these machines caught my eye. It showed a website I know pretty well – Facebook! But it wasn’t the Login screen – as it should be – but the profile page of a member. Someone had forgotten to logout of his or her account. Anyone in this airport would now have full access to all data and – of course – be able to write status messages on the profile page of the account owner and all people in the friendlist – which could harm this person‘s reputation. Which is a bad thing!
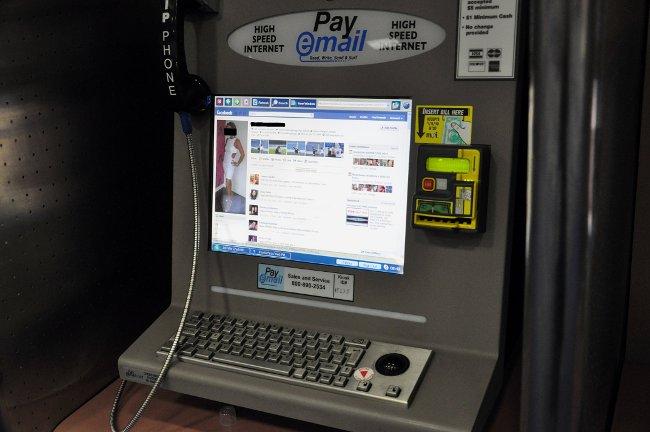
But even worse: you never know if these machines have been compromised. Malware might spy on personal information, login credentials or other sensitive data. IT vs car comparisons do not always hit the nail on the head, but I’ll give it a try. Airport kiosks (as well as all other kiosk machines) are like rental cars. Some people use it in a reckless manner because it’s not their property – in terms of cars it means aggressive driving, in terms of computers it’s abandoning security awareness. And you don’t even know if a security solution is installed on the system.
It’s okay to use such systems in the way they’re actually meant: checking travel information or reading news, but never use them in way that means you’d need to disclose sensitive information. If you need to check your e-mails, Facebook and the like, use your own device. Airports usually offer hotspots you can use (in the case of Mc Carran it’s even free!). If you need more information on secure browsing while on the road, you might want to read the article “Summertime is wireless time“ here on Securelist.
Have a pleasant, safe and secure journey!




















Airport Security – On a Different Angle Though …