
Adobe released its fix for CVE-2011-0609 this afternoon, making good on last week’s advisory dealing with the latest Flash zero-day. Kaspersky Lab products detected the variants as “Trojan-Dropper.MSExcel.SWFDrop” this past week.
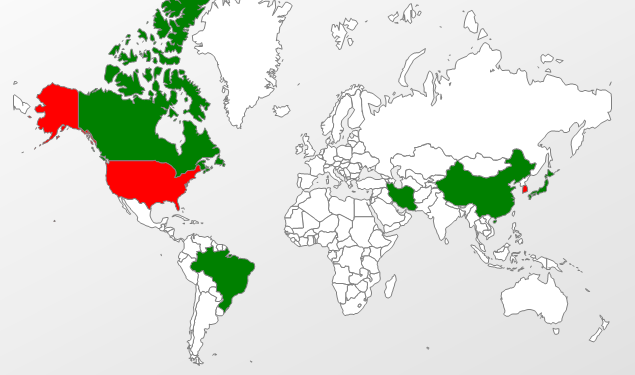
While we questioned the usefulness of Flash functionality within Excel spreadsheet cells last week, attackers were sending out emails containing just these sorts of files. Our Kaspersky Security Network statistics saw very low numbers spread out across the globe, revealing attackers making targeted use of this zero-day attack.
While there were few attacks seen using this unusual mix of a Microsoft Office and Flash implementation, a question remains, why do Adobe patches continue to take so long to roll out at this point?
On one hand, we saw Google Chrome’s update for the same flash vulnerability roll out almost immediately last Tuesday, in part because of Chrome’s close integration with Flash. The Chrome dev team brags security – it’s in their browser design and security is a major part of their process. Chrome security updates are clean, easy and quick.
On the other hand, the rest of the world using Flash (which is almost 99% of internet connected PC’s, according to Adobe) was browsing with vulnerable software and provided some complicated options as attackers set their crosshairs on their next high-value target. At the same time, Flash is one of the most vulnerable applications on the web, meaning users have not been updating their software – its many versions of updates aren’t necessarily clean, easy or quick.
Adobe’s sandbox was a step in the right direction for Reader X. But attackers are responding with improvements in their own offenses. A sandbox delays exploitation, it doesn’t end exploitation – this month, Stephen Fewer
won pwn2own with an attack chaining 3 exploits together to pop out of Internet Explorer’s sandbox and compromise a Windows 7 system also protected by DEP/ASLR. In the meantime, we welcome more improvements and speed to this inevitable patching process. And please update your Adobe Reader, Flash, and Acrobat software to the latest versions.





















Adobe Fix for CVE-2011-0609