
As I was saying in yesterday’s blog post, we were expecting the number of Koobface C&C servers to start growing sometime this week:
“Cybercriminals don’t want the number of C&C servers to drop too much, as that would mean losing their control over the botnet. So, if the earlier strategy of the Koobface gang is anything to go by, we should be seeing new servers being added to control the botnet soon, most probably this week.”
And, guess what? Yesterday evening the Koobface gang started adding new servers:
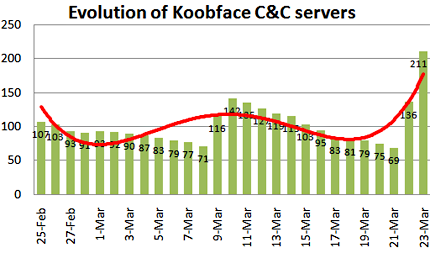
The total number of active Koobface C&C servers went from a low of 65 yesterday to over 200 at the time of writing – 225, to be precise. This is the most Koobface C&C servers we’ve ever seen in a 24-hour period, and we keep discovering new ones.
We’ve already started contacting the owners of the compromised websites to get the C&C servers taken down and cleaned up as quickly as possible.






















Active Koobface C&C servers hit a record high – 200+ and counting