
Cyber-criminals in Brazil and the wider Latin America region almost always use social engineering tricks to launch attacks. Sometimes, they send fake bank e-mails or e-mails from popular Internet services. The e-mail databases of the potential victims are being compiled based on the stolen e-mail addresses from the infected machines and particularly from the addresses stored in e-mail clients.
Once the e-mail addresses are compiled, the fraudsters use several external tools like PHP shells on hacked Web servers.
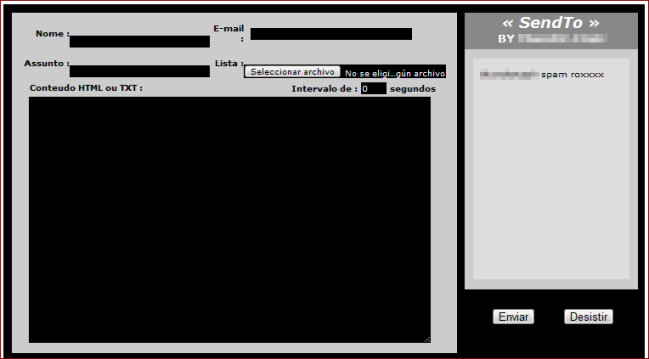
During my daily analysis, I found an interesting shell for mass mailing. The code shows it was developed locally in Brazil:
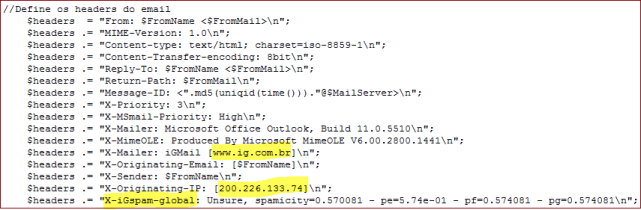
By editing the original PHP code, the criminal can fake the “original headers” of the messages they send. Very interesting.
Now let’s check the original IP address of the mentioned domain:
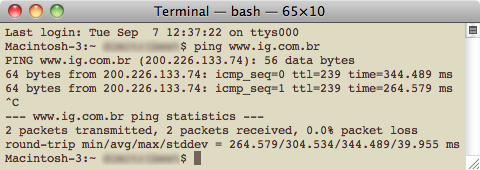
As you see in this case, the criminals are sending fake e-mails using the identity of IG (www.ig.com.br) a very popular Internet resource in Brazil. They fake the mailer, the original IP address and even the Spam scoring. So, there is a big probability this e-mail will be delivered usefully to the victim, bypassing anti-spam filters. Even the most experienced IT people can be tricked into believing that the message came from IG.
During analysis of the code, I discovered another interesting bit of information related to the shell. The server was hacked by a famous defacer from Brazil (name withheld during this investigation) who is quiet active and notorious around the world. On
September 7th alone, he/she defaced 42 different domains.
In the past, we’ve seen Web defacers act with only with political motivation. That has now changed. The Web defacers are being
used by the online money gangs as a part of outsourced services.






















A Web Defacer Turns to $$ Spam Fraud