
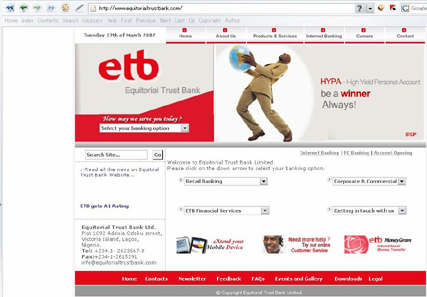
We’ve just come across a neat little phishing attack. The Equitorial Trust Bank seems to have a few issues with server security. Of course, the fact that the bank is located in Nigeria might ring a few warning bells, and we’re looking into this.
Currently, however, the bank doesn’t seem to have noticed the Easter egg that they’re hosting – a phishing page for eggTM banking customers.
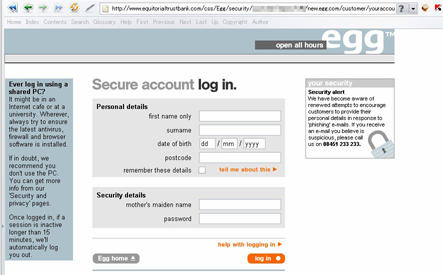
The eggTM page differs from the legitimate eggTM log-in page only in the colours that it uses. Sadly, we know from experience that users often don’t notice differences like that.
Of course, we’ve notified the bank, and maybe they’ll be more security conscious in future.





















A Nigerian Easter egg