
Today my colleague Jorge Mieres found some interesting information related to the new HLux botnet.
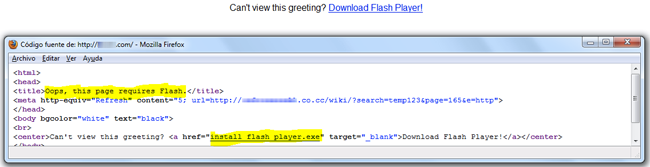
This new worm is propagating via e-mail with a backboned administration through a crimeware pack called BOMBA. The scam messages come with a message to a fake eCard requiring installing Flash Player (an old scammers trick).
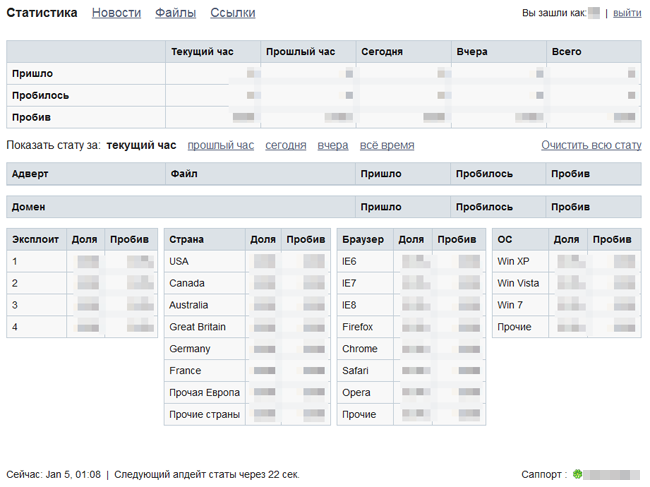
After the infection, the newly installed malware downloads a malicious update which is detected by Kaspersky as Email-Worm.Win32.Hlux.c and establishes a connection with BOMBA’s server reporting statistics about the infection.
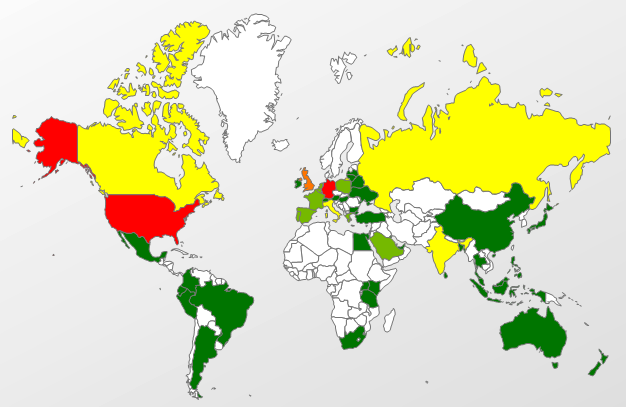
Our statistics for Jan 5 show countries with the highest infection attempts are the U.S., Germany and the U.K.
We’ll keep researching this issue and will keep you updated.






















A few words about the HLux botnet